How to ensure AI compliance when automating business processes
AI-powered automation has moved well beyond chatbots and simple Q&A. Today's enterprise AI systems can draft customer responses, update records, close support tickets, and trigger multi-step workflows across dozens of business applications. That shift—from answering questions to taking actions—fundamentally changes the compliance equation.
Regulations like GDPR, the EU AI Act, HIPAA, and sector-specific rules in finance and healthcare already govern how organizations collect, process, and act on data. When an AI agent executes a workflow that touches personal information, financial records, or employee data, every step in that chain becomes subject to the same legal and ethical scrutiny as a human decision. The stakes are higher, and the margin for error is smaller.
This guide breaks down what AI compliance actually means in the context of business process automation, and provides a practical framework for building automations that are useful to the business and defensible to auditors. Each section covers a specific phase—from scoping and governance to privacy controls and audit readiness—so teams across engineering, IT, security, and compliance can move forward with confidence.
What is AI compliance when automating business processes?
AI compliance when automating business processes means every AI-driven workflow follows the laws, industry rules, and internal policies that apply to your organization—while remaining secure, explainable, and auditable. In practice, this covers data privacy, access control, human oversight, and documentation from the design phase through daily operations. It is not limited to model safety or responsible AI principles in the abstract; it extends to how data is accessed, how decisions are made, and how work gets executed end-to-end.
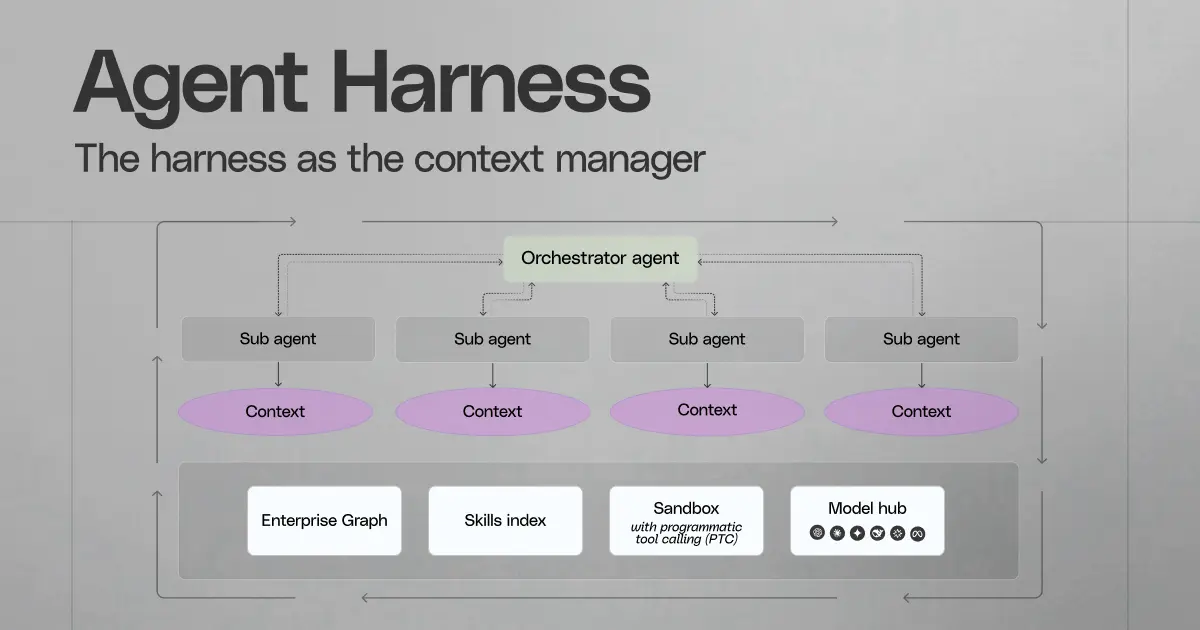
The distinction matters because automation raises the bar. A conversational AI assistant that surfaces a document is one thing. An agentic system that reads a support ticket, queries a knowledge base, drafts a response, and closes the case is something else entirely. Once AI can take actions—not just answer questions—organizations need stronger guardrails, clearer ownership, and better evidence that the right thing happened at every step. The goal is to ship automation that accelerates the business without creating hidden risk or undocumented decision-making.
Key concepts in this guide
Several terms appear throughout this article, each representing a distinct layer of the compliance program:
- AI compliance regulations: The external legal and regulatory requirements that apply to your organization—GDPR, CCPA, the EU AI Act, HIPAA, SOX, and sector-specific rules in finance, healthcare, and beyond.
- Enterprise AI compliance frameworks: The internal structures you build to operationalize those requirements—risk assessment templates, approval workflows, evidence standards, and vendor review processes.
- AI governance strategies: The organizational decisions about who can approve, modify, or retire an AI automation, and under what conditions.
- AI audit processes: The mechanisms you use to prove compliance—audit trails, testing protocols, sampling reviews, and incident documentation.
- AI transparency measures: The practices that allow users, reviewers, and regulators to understand what an AI system did, what data informed its output, and why a particular action was taken.
What "good" looks like in an enterprise setting
Mature AI compliance programs share a few characteristics. Permission-aware access to company knowledge is non-negotiable; the automation should never bypass existing access controls or surface data a user isn't authorized to see. Data minimization keeps the scope tight—each workflow should use only the information it genuinely needs. Human oversight applies where it matters most, especially for high-impact outcomes like hiring decisions, financial approvals, or customer-facing communications. And compliance is continuous, not a one-time signoff before launch.
Where this commonly breaks
Enterprise deployments reveal recurring failure points that policy documents alone won't catch:
- The retrieval layer quietly expands access. When AI automations rely on enterprise search and connectors to pull context from dozens of systems, the retrieval layer can inadvertently surface content that the requesting user shouldn't see—unless it enforces existing access control lists and permissions end-to-end, at query time, for every request.
- Connectors become an uncontrolled data path. Each connector that authenticates into a SaaS application, document store, or database represents a potential data egress point. Without careful evaluation of how connectors authenticate, scope their access, log activity, and restrict downstream use of retrieved content, organizations risk accidental overexposure of sensitive information.
- Teams treat AI as "just a UI." Agentic systems don't just display information—they act across tools. A single workflow might read from a ticketing system, query a CRM, draft an email, and update a finance record. That cross-system action scope demands explicit action controls, destination allowlists, and end-to-end auditability that a simple chat interface never required.
These failure modes are not theoretical. They reflect real patterns observed in enterprise AI deployments across technology, financial services, and professional services organizations—exactly the environments where the cost of a compliance gap is highest.
How to ensure compliance when automating business processes with AI?
Treat compliance as a managed program with lifecycle artifacts
Make AI compliance a formal program with named owners, required artifacts, and repeatable review gates. Tie each automation to a defined record set: use-case intent, risk tier, data categories, action scope, vendor terms, and a control plan that maps to your internal policies and external obligations.
Use established enterprise AI compliance frameworks to structure that program. NIST AI RMF supports consistent risk work across “map, measure, manage,” while ISO/IEC 42001 adds management-system discipline—roles, documentation, internal audit cadence, and corrective actions—so the program holds up across business units and reorganizations.
Start small; scale based on evidence, not optimism
Early success comes from careful selection, not broad ambition. Pick workflows that deliver clear operational value while keeping exposure low—narrow data scope, limited user population, and reversible outcomes.
A practical starter set usually includes:- Internal drafting support: Text drafts for knowledge articles, ticket replies, or status updates; a human owns final approval and delivery.- Read-only assistance for knowledge work: Context assembly from approved repositories with strict source boundaries; no record edits.- Triage support for queue work: Suggestions for routing, severity, or category; supervisors retain control over assignment rules.
After the first set reaches stable performance, convert lessons into standard assets: a shared intake form, a risk rubric, a DPIA-style worksheet for personal data, and a “go-live” checklist that teams can complete without bespoke review cycles.
Anchor on three outcomes that produce audit-grade evidence
Compliance debates move faster when the program aims at outcomes that create proof, not promises. Treat these as non-negotiable acceptance criteria for every automation:
- Authorized data use, with verifiable controls: Evidence should show exactly which identity accessed which system, under what authorization context, and which data classes entered the workflow. Capture entitlement snapshots or access assertions per run where feasible; enforce purpose limitation through explicit allowlists for sources and fields.
- Action scope that stays explainable under review: Define allowable actions at the workflow level—draft, recommend, execute—and bind each to approval rules, pre-flight checks, and destination constraints. Store the rationale for any override so compliance teams can audit exceptions as first-class events.
- Reproducible runs across time, versions, and vendors: Logs should include workflow version, model/provider identifier, prompt template version, retrieval references, and action payloads. That record must support root-cause analysis after incidents, policy updates, or regulatory inquiries.
Add an enterprise data and connectors review early
Connector design often determines whether an automation stays inside policy boundaries. Treat connectors as controlled interfaces to systems of record, with explicit acceptance tests and ongoing change oversight.
A connector review should validate:- Credential governance: Clear ownership, rotation policy, and scope boundaries for tokens, keys, and service roles.- Permission fidelity tests: A regression suite that validates access parity between the source application and the automation path across representative roles and groups.- Data residence and retention posture: Location constraints for processing and storage, plus retention rules for prompts, outputs, and retrieved context.- Audit event completeness: A run record that captures access events, admin changes, connector config updates, and downstream write operations in a form auditors can use.- Operational guardrails: Rate limits, throttles, and failure controls that prevent cascading actions during upstream outages or unexpected input patterns.
Use a consistent vendor and connector questionnaire to keep reviews uniform across new systems, acquisitions, and regional rollouts; some teams borrow a nine-question enterprise connector rubric from vendors such as Glean as part of procurement due diligence.
Align requirements with how CIOs evaluate workplace agents
CIO evaluation tends to focus on architecture choices that reduce operational surprise: secure default access patterns, relevance grounded in sanctioned enterprise content, and administrative control that supports policy enforcement at scale. Translate that into enforceable requirements—central policy administration, role-based build permissions, change control for new data sources or action types, and production oversight that flags drift, exception spikes, or abnormal action volume.
Define “compliant automation” as measurable operational behavior: stable controls under change, clear ownership per workflow, and evidence that holds up under audit sampling across departments and regions.
Frequently Asked Questions
What are the key regulations governing AI in business?
The applicable rules depend on geography, data category, and decision impact. In practice, most enterprises face a blend of privacy law obligations (personal data use), sector obligations (healthcare, financial services), consumer protection rules (truthful product claims and harm prevention), and AI-specific requirements in certain regions.
A useful way to scope requirements is to map obligations to the workflow’s “regulated moments,” not to AI as a feature:- Collection and reuse: limits on what data enters the workflow, why it enters, and how long it stays available to the system.- Disclosure duties: what you must tell employees, customers, or candidates when AI influences an outcome; this often covers notice, contact points, and documentation that supports review.- High-impact decision safeguards: additional controls when automation can affect employment, access to services, financial outcomes, or health outcomes; these controls usually require oversight, documented instructions for use, and proof that the system operates as intended.- Provider and procurement requirements: contractual and operational expectations that restrict secondary use of enterprise data and define retention, breach notice, and audit rights.
How can organizations implement AI while ensuring compliance?
Implementation works best when teams treat each automation as a controlled product release with explicit “definition of done” for compliance. That definition should cover data rights, operational controls, and documentation that supports later review without forensic work.
A practical rollout sequence that avoids common compliance traps:1. Create an AI automation inventory first: list use case purpose, impacted users, systems touched, and whether the automation can change a system of record. This inventory becomes the backbone for privacy records, approvals, and audit planning.2. Run a structured impact assessment: for workflows that touch personal data or meaningful outcomes, use a DPIA-style assessment to document purpose, data categories, retention, third-party processing, and mitigations.3. Separate “recommendation” from “execution” in system design: treat execution rights as a distinct capability with tighter release gates, stronger operator controls, and stricter post-release review.4. Enforce procurement-grade connector acceptance: validate connector scope behavior, admin guardrails, and access log completeness before any workflow touches production repositories.
What best practices should be followed for AI compliance?
Compliance holds when the program answers three operational questions for every run: what data entered, what constraint applied, and what action occurred. Best practice focuses on controls that keep those answers stable through change—vendor updates, permission churn, and shifting data quality.
Practices that tend to reduce audit and incident risk in real deployments:- Data quality assertions for critical fields: define required fields and acceptable ranges for inputs that drive downstream action (customer tier, contract status, payment state). Block execution when required fields fail validation rather than allow the model to infer.- “Claims governance” for user-facing capabilities: align product messaging, internal enablement, and system behavior so the organization avoids misleading statements about what AI does, what it guarantees, and what oversight exists.- Evidence-grade exception handling: treat exceptions as first-class outcomes with reason codes, accountable owners, and time-bounded remediation tasks. This prevents a slow drift toward informal overrides.- Post-change safety checks: require targeted regression tests after schema changes, connector updates, or workflow template edits—especially for outbound communications and record updates.
What tools or frameworks can assist in maintaining compliance with AI?
Frameworks provide the structure; operational tooling provides enforcement and proof. Most enterprises get the most leverage from a small set of integrated capabilities that support continuous control evidence, not one-off reviews.
Tool categories that support durable compliance operations:- GRC and policy workflow systems: intake, approvals, exception records, and a living registry of automations with ownership and scope boundaries.- Data discovery and classification: consistent tagging of sensitive fields across repositories so workflows can apply domain-specific restrictions without manual curation.- Identity and privileged access controls: role-based build permissions, elevated access workflows for connector administration, and periodic access recertification for workflow owners and approvers.- Security telemetry and alerting: centralized audit events for connector access, configuration edits, and high-impact actions, plus alert rules that detect abnormal access patterns and outbound activity spikes.- Evaluation and release gating: test harnesses that measure task accuracy, refusal behavior, and policy adherence on representative cases before any change reaches production.
How do organizations audit AI systems for compliance?
Audit should focus on control effectiveness for the workflow, not subjective judgments about model “intelligence.” A strong audit method checks whether the organization can demonstrate authorized access, proper oversight, and traceable outcomes across a representative sample of runs.
A practical audit approach that fits enterprise internal audit methods:1. Confirm scope and classification: verify that the workflow’s documented purpose, risk tier, and action scope match what production configuration allows.2. Test access control with reconciliation: compare workflow access events to source-system access records for the same identities and time windows; discrepancies often reveal permission bypass, over-scoped service roles, or incomplete logs.3. Inspect decision and action records: validate that each sampled run includes the required artifacts—approval events where required, policy state at time of run, and a clear record of downstream writes.4. Review vendor and processing evidence: confirm data retention settings, contractual restrictions on secondary use, and security attestations that support enterprise requirements for third-party processing.5. Re-test after material changes: repeat targeted audit tests after new data domains, new write targets, jurisdiction expansion, or provider/model changes; these changes often alter obligations even when the workflow intent stays the same.
AI compliance isn't a milestone you reach — it's an operational discipline you maintain through every workflow change, every connector update, and every regulatory shift. The organizations that get this right treat compliance as a design input from day one, not a review gate at the end.
If you're ready to build AI-powered automation on a foundation your security, privacy, and compliance teams can stand behind, request a demo to explore how we can help transform your workplace.