Top 7 industries with stringent AI compliance needs in 2026
AI compliance regulations have moved from abstract policy discussions to operational reality. In 2026, frameworks like the EU AI Act, NIST AI Risk Management Framework, and ISO 42001 carry real enforcement weight — and organizations that treat compliance as optional risk losing market access, facing steep penalties, or eroding customer trust.
For regulated industries, the stakes are even higher. AI-driven decisions in healthcare, finance, government, and critical infrastructure can directly affect human health, financial stability, legal rights, and personal safety — making robust governance not just a legal obligation but an ethical imperative.
This guide breaks down the seven industries with the most stringent AI compliance needs in 2026, the specific regulations shaping each sector, and the practical strategies enterprise teams need to build governance programs that scale.
What does AI compliance mean for regulated industries?
AI compliance refers to the body of laws, frameworks, and standards that govern how organizations build, deploy, and monitor AI systems. At its core, the goal is straightforward: ensure AI operates safely, ethically, and transparently. In practice, that translates to documented risk management processes, bias testing, data governance controls, explainability requirements, and mechanisms for human oversight — all enforced by regulators with increasing specificity.
The principles underpinning most AI compliance regulations converge on a consistent set of expectations:
- Transparency: Organizations must clearly disclose how AI systems function, what data they use, and what limitations they carry.
- Fairness: AI outputs cannot produce discriminatory results across protected demographic groups — a requirement that demands proactive bias testing and ongoing monitoring.
- Accountability: Clear ownership chains must exist for AI system outcomes, with defined escalation paths when something goes wrong.
- Data privacy: Personal and sensitive information used by AI must be handled under strict consent, access, and retention controls aligned with regulations like GDPR and HIPAA.
- Human oversight: Automated decisions — especially those affecting individuals' rights or safety — must include fail-safe mechanisms and the ability for qualified humans to intervene.
These principles are not aspirational. By 2026, major governance frameworks have matured into enforceable standards. The EU AI Act classifies AI systems into risk tiers — from banned applications like social scoring to high-risk categories that require conformity assessments, public registration, and lifecycle documentation before deployment. The NIST AI RMF provides a structured, repeatable methodology for identifying and mitigating AI risks across the system lifecycle. ISO 42001 establishes management system requirements with certification pathways that demonstrate regulatory readiness across multiple jurisdictions. Together, these frameworks make compliance a prerequisite for market participation, not an afterthought.
Compliance also does not exist to slow adoption — it exists to navigate the risks that come with deploying AI in high-stakes environments. As enterprise AI adoption accelerates across finance, HR, customer support, and IT operations, the attack surface for compliance failures grows in parallel. Every new AI tool introduced into a workflow — whether a chatbot handling sensitive customer data or an agent automating multi-step processes — must satisfy the same governance standards as the systems already in production. Organizations that embed compliance into the AI lifecycle from day one, rather than retrofitting it later, position themselves to adopt AI confidently while maintaining the trust of regulators, customers, and employees alike.
Why AI compliance needs vary across industries
Data sensitivity sets the baseline
Compliance scope starts with the data class and the rulebook attached to it. A system that touches PHI, cardholder data, controlled unclassified information (CUI), or bulk electric system cyber assets inherits sector mandates that dictate storage controls, access paths, retention, and evidence.
A practical way to map “sensitive” to real obligations:
- PHI and clinical records (HIPAA; often plus FDA or EU MDR/IVDR depending on use): policy must cover minimum necessary access, strict audit evidence for disclosures, and controls around downstream reuse of patient context.
- Payment and financial account data (PCI DSS; plus SOX and supervisory expectations for risk controls): teams must prove data segregation, controlled access for service accounts, and traceable decision records that support examiner review.
- Defense and government data (NIST 800-171, CMMC, FISMA, ITAR): requirements extend beyond privacy into procurement readiness, supplier controls, and limits on where data can reside and who can access it.
Decision impact determines the risk tier
Regulators and auditors focus less on model sophistication and more on outcome severity. The same underlying technique can produce low-stakes convenience in one workflow and a legally consequential decision in another—credit access, clinical prioritization, benefits eligibility, employment screening, or identity verification.
In practice, decision impact shifts compliance expectations in three common ways:
- Rights and access decisions: credit scoring, insurance underwriting, hiring screens, and public benefits workflows require clear adverse-action rationales and defensible records for disputes.
- Safety and reliability decisions: clinical decision support and critical infrastructure control use cases pull in safety engineering norms—validation, change control, and post-release performance checks that match the environment’s tolerance for failure.
- Security and fraud decisions: AML and fraud controls demand explainable triggers, consistent thresholds, and reproducible outputs that withstand audit sampling and supervisory review.
Regulatory bodies shape the control set
“Regulated industry” does not mean one standard. Each sector adds its own compliance shape: medical device oversight pushes formal validation and post-market controls; financial regulators push model risk management discipline; energy regulators push operational resilience and cyber controls; public sector procurement pushes certification and supplier proof.
Across sectors, the evidence package tends to differ by regulator posture, not by AI architecture:
- Finance examiners expect a model inventory, validation artifacts, change approvals, and monitoring reports that align with established model governance practices.
- Healthcare regulators expect clinical safety rationale, dataset governance, traceability from inputs to outputs, and controls that protect patient data throughout every workflow step.
- Energy and utilities expect alignment with cybersecurity and reliability mandates such as NERC CIP—access controls, segmentation, and audit records that match operational technology constraints.
- Government buyers expect compliance attestations up front, often as a prerequisite for deployment authorization inside restricted environments.
Geography adds overlap, friction, and timing pressure
Cross-border operations create a compound rule set: EU horizontal rules, national privacy laws, sector regulators, and U.S. state-level requirements that evolve on different timelines. The U.S. pattern—agency guidance plus state laws—often forces companies to design for variability, while EU obligations can apply to any provider that serves EU users, regardless of headquarters location.
Many global teams standardize on a single internal control baseline, then layer jurisdiction-specific requirements on top—especially for disclosure language, record retention, and automated decision rights.
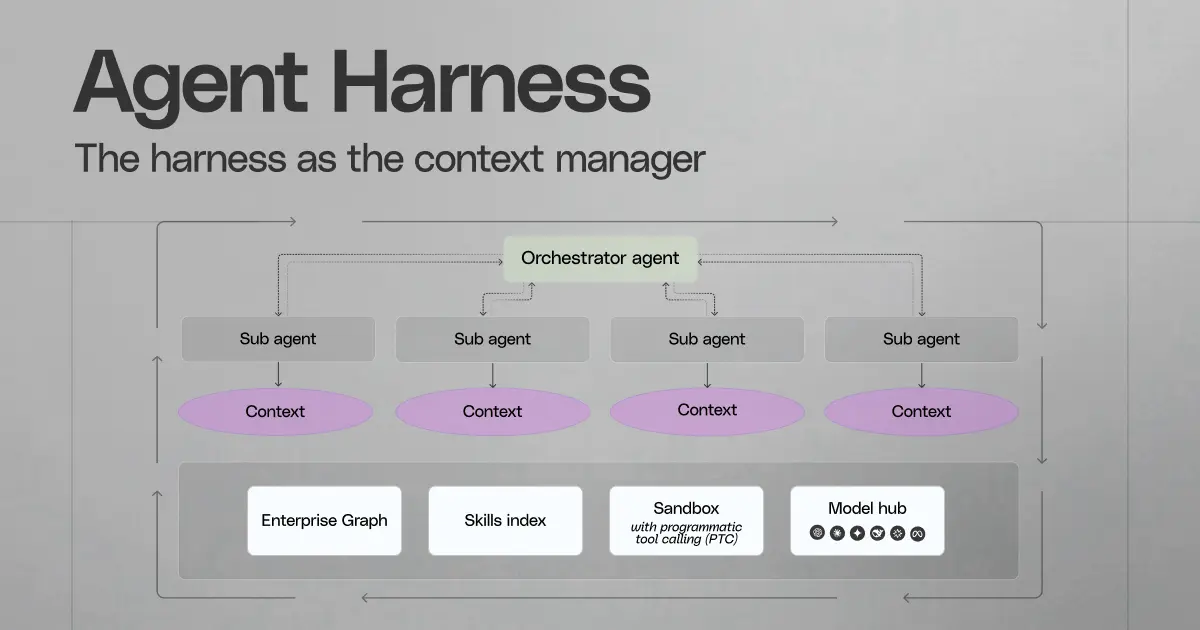
Workflow automation raises the bar beyond the model
As AI shifts from content generation to multi-step task execution, compliance must cover workflow mechanics, not just output quality. Agentic systems can read from one system, transform context, then write into another—actions that trigger segregation-of-duties concerns, record integrity requirements, and heightened audit expectations in regulated environments.
For agent-based automation in finance operations, healthcare administration, and public-sector case work, governance needs to cover:
- Identity design for actions: clear ownership of service accounts, constrained scopes, and enforced separation between read privileges and write privileges.
- Transaction-grade evidence: immutable logs that capture tool calls, data sources referenced, and every downstream change made by the system.
- Policy-aligned approvals: “four-eyes” checkpoints for sensitive writes—payment changes, patient record updates, eligibility determinations—so humans retain formal responsibility for high-impact actions.
- Integration discipline: consistent control strength across connectors so one weaker integration does not become the path around stronger controls, including platforms such as Glean.
Financial services
Financial institutions sit at the intersection of data protection law, prudential oversight, and consumer protection expectations. That mix creates one of the most demanding AI compliance environments in 2026—Basel III for capital and risk discipline, SOX for financial reporting controls, PCI DSS for card data environments, plus supervisory guidance from regulators such as FINRA and the Federal Reserve.
AI use in this sector rarely stays “internal.” Systems that influence fraud disposition, AML casework, credit decisions, or trading controls affect customer outcomes and market integrity, so governance must cover both risk operations and customer-facing experiences with the same rigor.
The compliance stack finance teams must satisfy
Finance AI governance programs must map controls to the frameworks auditors and examiners already use. The practical implication: an AI system needs the same operational proof as any other regulated control—ownership, documented design, evidence of testing, and controlled change.
Common expectations that show up across exams and internal audit reviews:
- Lifecycle governance that matches model risk discipline: a formal inventory, clear accountability, independent validation, approved releases, performance review cadence, and retirement criteria.
- Decision documentation that supports dispute and review: artifacts that explain why the system produced a given recommendation or score, tied to the exact version and data context used at that time.
- Customer protection guardrails: defined review requirements for adverse outcomes, with recorded justification when staff accept, override, or reject an AI-driven recommendation.
High-scrutiny AI use cases in finance
AI shows up in several workflows that regulators already treat as high consequence. Each use case drives a distinct evidence burden:
- Fraud and transaction anomaly controls: teams must show alert rationale, test coverage across known fraud typologies, and disciplined tuning practices so changes do not degrade detection or inflate false positives.
- AML and sanctions workflows: systems must support case reproducibility for audit sampling—what signals triggered the alert, what context the analyst saw, and what steps led to disposition.
- Credit scoring and risk assessment: policies must require explainability suited to adverse action review, plus bias assessment across protected classes and correlated attributes that can create proxy discrimination.
- Algorithmic trading and surveillance controls: governance must cover stress behavior, outlier handling, and controls that prevent unsafe execution patterns during volatility.
EU AI Act implications for credit and risk tools
Under the EU’s risk-based framework, certain finance systems—especially creditworthiness and risk assessment—fall into high-risk classes. That status brings a heavier operational load than a typical internal analytics tool: pre-deployment evidence packages, formal quality controls, and ongoing obligations that regulators can inspect.
In practice, teams should expect requirements such as:
- Structured technical documentation that a compliance team can hand to reviewers without reverse engineering experiments or notebooks.
- Data governance evidence that covers provenance, quality checks, and suitability for the intended population and decision context.
- Post-release oversight that proves performance stability over time, with defined triggers for retraining, rollback, or additional human review.
Agent use cases in finance: controls must follow the workflow
As finance teams adopt agents for reconciliation support, close coordination, audit request fulfillment, and customer operations, the primary compliance risk shifts from “what the model says” to “what the system changes.” Multi-step automation can touch financial records, customer communications, and evidence repositories in one flow, so controls must govern the full toolchain.
Controls that hold up under audit and examiner review:
- Privilege design that matches existing control matrices: tight scopes for data access, explicit separation between preparation steps and approvals, and clear ownership for every automation identity.
- Tamper-resistant audit trails for each step: event records that capture source systems used, transformations applied, outputs produced, and any downstream updates, tied to the responsible identity and time.
- Approval gates for sensitive actions: mandatory human review for high-impact writes—payment instructions, ledger adjustments, customer disposition changes—based on policy, not convenience.
- Change control for agent workflows and prompts: versioning, peer review, test plans, and rollback procedures for prompts, routing logic, and tool permissions so governance stays stable as workflows evolve.
Healthcare and life sciences
In healthcare, AI compliance sits close to patient safety, not just data privacy. A weak control can show up as a missed abnormality, a delayed escalation, or an unsafe message to a patient.
Life sciences teams also place AI inside regulated documentation flows—study reports, safety narratives, label content, and clinical evidence packages. That reality forces disciplined controls around source material integrity, review rights, and record retention.
The regulatory spine: privacy, device oversight, and clinical-grade quality
Healthcare and life sciences programs often sit under multiple oversight regimes at once. The compliance pattern depends on whether the system supports clinical decisions, supports operations, or meets the definition of regulated medical software.
Key regulatory drivers that shape requirements in 2026:
- HIPAA (U.S.): PHI access restrictions and safeguard requirements extend to AI features that summarize charts, draft patient communications, or surface clinical context. Business Associate Agreements, minimum-necessary controls, and security-rule safeguards often become gating items for vendor selection and internal rollouts.
- FDA oversight for AI/ML in Software as a Medical Device (SaMD): when AI functionality crosses into medical device territory, teams need evidence of clinical performance, defined intended use, and disciplined control over model updates so the released behavior stays consistent with validated claims.
- EU MDR/IVDR: for clinical tools in the EU, medical device rules can require structured clinical evaluation and formal quality practices that support a CE mark, plus documentation that stays aligned with real-world performance.
- EU AI Act (health-related high-risk categories): many clinical use cases fall into regulated risk classes, which can introduce additional obligations around dataset suitability, provider instructions, and operational controls that support safe use in clinical environments.
This stack creates a practical mandate: clinical AI needs documentation and controls that clinicians, compliance leaders, and regulators can all read and evaluate without guesswork.
Where AI shows up in care delivery—and what teams must control
Healthcare organizations deploy AI across clinical and operational workflows, but each category creates a different failure mode. Compliance work should map to those failure modes, not to the model type.
Four common deployment patterns and the specific governance pressures each creates:
- Imaging and diagnostic support: performance must hold across devices, sites, and patient populations. Teams often need site-level validation plans, thresholds for acceptable sensitivity and specificity, and controls that prevent use outside the cleared clinical context.
- Predictive clinical risk models: a model that flags deterioration or sepsis can change care escalation. Governance needs explicit clinical pathways—who reviews alerts, what action follows, and what rules prevent alert fatigue or silent failure.
- Administrative automation inside clinical systems: note drafts, coding support, and prior authorization assistance can affect billing integrity and clinical record quality. Controls must prevent propagation of incorrect content into the legal medical record and must preserve institutional documentation standards.
- Life sciences: safety and research workflows: AI that supports adverse-event detection, literature review, or regulatory writing must preserve source fidelity. Review protocols need clear attribution to primary evidence so regulatory teams can defend claims during inspection.
2026 operating expectations: disclosure, consent boundaries, and supervised care
In the U.S., state-level requirements increasingly push transparency into patient-facing workflows. Care delivery teams may need plain-language disclosure when AI contributes to communications or care support, plus an easy path to a human clinician when the interaction carries clinical consequence.
In the EU context, healthcare organizations often face dual obligations—medical device expectations plus AI governance expectations—within the same deployment. That reality pushes tighter alignment between clinical governance committees, privacy offices, and security teams so release approvals reflect both patient safety duties and statutory requirements.
Workflow agents in healthcare: safe automation needs clinical constraints
Agent-style automation can coordinate referrals, prepare discharge materials, or draft patient messages, but the system behavior must match clinical operating norms. The strongest programs treat these systems as clinical workflow components, not as generic productivity tools.
Safeguards that reduce operational risk without duplicative controls:
- Default-to-draft behavior for patient-facing content: the system can propose, but staff must explicitly accept before any patient communication leaves the organization.
- Clinical context minimization: the workflow should pull only the elements required for the task—problem list items, medication names, appointment details—rather than full-chart context by default.
- Structured output formats for EHR compatibility: templates and constrained fields reduce the chance of free-text errors that slip into the record and reduce review burden for clinicians.
- Downtime-safe design: when source systems fail or data access changes, the workflow should degrade into a clear manual path, with explicit guidance for staff so care continuity stays intact.
Government and defense
Public-sector AI programs operate under tighter constraints than most commercial deployments because they combine high-consequence decisions with strict rules for information handling. In 2026, compliance pressure increases further as the EU AI Act sets explicit high-risk categories for law enforcement, border and migration control, and justice-related systems.
Defense contractors and government agencies also face a practical constraint that rarely exists elsewhere: the compliance boundary often changes by mission, dataset, and system enclave. A single AI capability can require multiple control profiles, each tied to the data domain it touches and the environment it runs within.
Compliance frameworks that define the operating boundary
Government AI compliance rarely starts with model selection; it starts with the system authorization model and the data regime attached to the program. Teams typically need a control map that aligns AI workflows to federal security baselines, defense supplier requirements, export-control obligations, and—when applicable—EU high-risk AI obligations.
Two patterns drive most of the work:
- Authorization-first deployment: AI features must fit inside an approved system boundary, with documented controls, change discipline, and defined operational roles that reviewers can validate.
- Risk-class alignment for regulated use cases: EU AI Act high-risk areas such as law enforcement, border control, migration, and justice systems bring formal requirements around risk management, technical documentation, and post-deployment oversight that exceed standard IT governance.
Data classification and access controls: precision matters
Government datasets rarely share one uniform sensitivity label, even inside a single agency. Classification, compartmentalization, and “need-to-know” rules can shift by case, source, and collection method, which makes context assembly for AI especially delicate.
Controls that reduce cross-domain error without blunt restrictions:
- Data labeling with enforced handling rules: clear tags on records, attachments, and extracted text so downstream AI steps follow the same handling limits as the source.
- Source provenance for every cited fact: an operator should see where an assertion came from, which dataset version it used, and what transformations occurred before the output appeared in a case file or report.
- Cross-domain boundaries by design: separate knowledge stores and separate execution paths for distinct data regimes, with explicit restrictions that prevent “helpful” reuse of context outside its authorized domain.
Procurement and deployment: proof before access
Government procurement teams often evaluate AI systems as operational capabilities, not as generic software—especially when the tool can influence investigations, eligibility decisions, or enforcement actions. That evaluation tends to demand evidence that the system can operate within government constraints on confidentiality, integrity, and accountability.
Procurement reviews commonly concentrate on three areas:
- Demonstrable governance artifacts: a complete system description, risk controls, operational responsibilities, and change control practices that fit public-sector oversight.
- Data use limitations: explicit commitments on retention, secondary use, and model improvement practices so sensitive program data does not flow into unintended destinations.
- Operational resilience evidence: defined behavior under degraded conditions—data source outages, revoked access, partial records—so staff can maintain continuity without silent failure.
Citizen-facing AI and law enforcement: fairness, transparency, accountability
In citizen services and enforcement contexts, the compliance burden extends into administrative process: case records, reviewability, and defensible rationale. Systems that influence policing workflows, benefits administration, or adjudication support often face heightened scrutiny because they can affect rights and access to essential services.
Governance practices that fit public accountability constraints:
- Decision trace aligned to policy: outputs should map to program rules and permissible factors, with a clear separation between factual support and system interpretation.
- Review-ready case files: the system should produce artifacts that support appeals, ombuds review, and oversight audits—structured, attributable, and consistent across cases.
- Controlled use of identity and biometric signals: where identity verification or biometric analysis applies, controls should limit scope to authorized scenarios, with documented safeguards and strict operational oversight consistent with EU AI Act constraints in sensitive domains.
Classified-data governance and AI workflow design
Classified and export-controlled contexts require AI workflow designs that prevent accidental context spread and reduce exposure to prompt injection and data contamination risks. The most robust architectures treat AI as a constrained component inside a secured operational process, not as a general-purpose interface to sensitive repositories.
Design choices that tend to hold up under inspection:
- Bounded context policies: strict limits on what the system can pull into context for each task type, with explicit exclusions for data classes outside mission scope.
- Release discipline for model and prompt updates: controlled promotion paths, isolated test environments, and validation criteria that reflect mission impact, not typical software release velocity.
- Operational controls for tool-based actions: clear separation between analytical support and system-side changes, with defined operator responsibilities and recorded authorization when workflows touch official records or external communications.
Legal and professional services
Law firms and professional services teams work inside a different constraint set than most enterprises: client confidentiality doctrines, privilege, and work-product protections shape what AI can see and how outputs can enter formal deliverables. AI use can speed up core work—document review, contract analysis, legal research, and case preparation—but it must fit the standards that courts, clients, and professional rules already enforce.
A visible failure mode has already surfaced in practice: fabricated or unsupported citations that slip into filings. Courts have sanctioned attorneys who relied on AI-generated legal authorities without verification, which reinforces a simple reality—responsibility for accuracy stays with the licensed professional.
Compliance drivers that show up in real legal workflows
Legal tech compliance requirements often come from a mix of privacy law, security attestations, and profession-specific guidance:
- GDPR and CCPA obligations: client and counterparty data can include personal information, which pushes strict handling requirements for intake, processing, and disclosure language in client agreements.
- SOC 2 expectations: corporate legal departments and procurement teams frequently require SOC 2 reports (or equivalent evidence) before they allow AI systems to touch sensitive matters.
- ABA cybersecurity guidance: firms use these guidelines to set a baseline for confidentiality safeguards, vendor evaluation, and incident readiness—especially for cloud-based tools used across matters.
- Court rules and judicial scrutiny: sanctions tied to unverified AI outputs signal an enforcement trend—courts expect attorneys to apply the same diligence to AI-assisted work as to any other work product.
Operational controls that match how legal teams work
The strongest programs treat AI as a support layer inside established legal workflows, not a shortcut around them:
- Matter-level intake rules: define which matter types allow AI assistance, what content types remain excluded (settlement strategy, expert notes, privileged investigations), and what client approvals apply under outside counsel guidelines.
- Discovery-aware handling for litigation work: align AI use with legal hold practices, protective orders, and redaction requirements so AI assistance does not create new production or disclosure risk.
- Research verification procedures: require citation checks through standard citators (Westlaw KeyCite, Lexis Shepard’s), plus source pull-through for any quotation, holding, or procedural posture referenced in a deliverable.
- Contract review standards that preserve intent: mandate attorney review for clause substitutions, fallback language, and negotiation positions; include playbook alignment so AI suggestions track the client’s approved risk posture.
- Vendor security and confidentiality review: assess tools against the firm’s security baseline and client requirements, with explicit contractual language on confidentiality and data use consistent with SOC 2-driven procurement norms.
Governance structures firms adopt without slowing delivery
Many firms now formalize oversight through lightweight but specific governance mechanisms:
- Internal AI ethics committees: a standing group that sets permitted use cases, reviews exceptions for sensitive matters, and resolves conflicts between productivity goals and client constraints.
- Practice-group protocols: tailored guidance for litigation, M&A, employment, and regulatory teams—each group faces different confidentiality pressures and verification needs.
- Quality checks inside review workflows: structured steps that ensure AI-assisted content passes cite-check, fact-check, and client instruction checks before it reaches a court, regulator, or counterparty.
Energy and critical infrastructure
Energy and utility teams deploy AI inside environments that prioritize stability, safety margins, and recoverability under stress. The compliance burden rises fast because the same organization often runs modern cloud analytics alongside legacy OT networks that operate with strict latency and availability constraints.
Sector oversight also looks different from typical enterprise IT. FERC and NERC expectations, plus reliability obligations and cyber audit cycles, shape what “acceptable AI” looks like—especially when a system touches control-room tooling, OT telemetry, or bulk electric system workflows.
NERC CIP realities: AI must align to OT boundaries, not just IT policy
NERC CIP does more than request “good security hygiene.” It defines auditable requirements around electronic security perimeters, system categorization, vulnerability management cadence, and configuration baselines for BES Cyber Systems—constraints that influence where AI can run, what it can see, and how it can connect.
Design implications that show up in real deployments:
- Perimeter-first architecture: AI components that ingest OT signals often need placement outside the electronic security perimeter (or inside with strict boundary controls), with carefully defined data paths from historians, SCADA, or ICCP links.
- Interactive remote access constraints: any AI feature that supports remote operations work must fit strict access patterns—jump hosts, multi-factor requirements, session controls, and explicit monitoring expectations.
- Baseline configuration enforcement: models and supporting services must fit configuration management and patch windows that reflect operational reality, not continuous-deploy defaults.
High-impact AI use cases in utilities and energy operations
Energy AI work often targets reliability, asset health, and operational awareness. The compliance posture shifts by workflow because each one changes what evidence auditors expect and what failure modes engineers must contain.
Use cases that trigger the most governance and engineering effort:
- Predictive maintenance on critical assets: transformer and breaker health models depend on sensor quality and consistent operating conditions; teams need defensible calibration practices across sites and clear criteria for “actionable” alerts versus informational signals.
- Grid planning and forecasting: load and generation forecasts can influence dispatch planning and outage preparation; governance needs clear assumptions, known limits (extreme weather, abnormal demand), and documented performance checks per season or operating regime.
- OT anomaly detection: anomaly signals can drive incident workflows in high-noise environments; teams need careful threshold design, documented triage procedures, and clear separation between security events and benign operational variation.
- Environmental and compliance analytics: models that support emissions, spill detection, or compliance reporting must preserve a chain from source measurements to reported outputs so reviewers can reconstruct how a number entered a filing.
Security proof and vendor onboarding: reliability-grade assurance beyond generic attestations
Utilities often require evidence that a vendor can operate inside reliability and cyber audit realities, not only inside standard enterprise SaaS expectations. CIP-013-style supply chain risk practices, plus utility security questionnaires and operational readiness reviews, tend to carry more weight than a single generalized report.
Artifacts that procurement and security teams commonly demand for AI systems that touch sensitive operational workflows:
- Remote access design documentation: session control approach, administrative access paths, and monitoring coverage—mapped to how operations teams actually access systems.
- Data flow and residency mapping: where OT-derived telemetry travels, where it rests, and what prevents lateral movement into restricted network zones.
- Operational support commitments: incident response coordination model, escalation SLAs that match grid operations, and explicit handling for vulnerabilities discovered in edge components.
OT embedded automation: deterministic safeguards and operational runbooks
As AI moves closer to OT decision paths, compliance scrutiny shifts toward operational safety engineering. Teams need clear boundaries between analytics, recommendations, and any system behavior that could influence control outcomes.
Practices that reduce compliance risk when AI sits near operational control:
- Advisory-first integration: AI can surface prioritized insights inside control-room tools, while established systems retain authority for setpoints and protective actions.
- Fail-closed behavior for degraded inputs: when telemetry gaps, sensor faults, or upstream system outages occur, the AI layer should default to conservative outputs with explicit uncertainty signaling, not synthetic completion.
- Runbook alignment: outputs should map to existing operating procedures—what action class applies, who owns the response, and what evidence the operator must record in the event timeline.
Insurance and telecommunications
Insurance
Insurance programs place AI inside decisions that affect coverage terms, premium levels, and claim outcomes. That puts underwriting and claims automation under close scrutiny from regulators and state insurance departments, especially when models use nontraditional signals such as consumer behavior data, device data, or third-party attributes.
By 2026, insurers face tighter requirements from multiple directions: U.S. insurance regulators have issued model guidance on insurer use of AI systems, the EU’s AI rulebook pushes elevated obligations for sensitive decision systems, and state-level AI laws such as Colorado’s impose formal duties for certain automated decisions. The net effect: insurers must prove consistent treatment across customer populations, maintain a clear line from permitted inputs to decisions, and keep records that stand up in market conduct reviews.
Key control areas that reduce regulatory exposure in underwriting and claims:
- Outcome disparity testing: measurement across statutorily protected attributes (and strong proxies) with documented mitigations when error rates or pricing deltas cluster in a way regulators would view as unfairly discriminatory.
- Decision basis records for adverse outcomes: a structured explanation package that ties coverage limits, non-renewal, pricing shifts, or claim denials to permissible factors and a specific model release.
- Release governance for rating and eligibility logic: versioned artifacts, pre-release evaluation, and a defined revert path when performance shifts after deployment or data inputs change.
- Manual sign-off triggers for sensitive cases: explicit thresholds that route unusual claims, hardship scenarios, or low-confidence outputs to licensed adjusters or underwriters, with recorded disposition reasons.
Telecommunications
Telecom compliance has two hard constraints: strict rules on subscriber data use and a large surface area for automation across networks and customer channels. In the U.S., FCC requirements for Customer Proprietary Network Information set limits on disclosure and use; in parallel, privacy obligations in Europe and U.S. states constrain how customer data can feed AI features.
AI programs in telecom often cluster into three operational zones, each with distinct governance needs:
- Network policy and capacity decisions: models that recommend configuration changes or traffic policies need controlled execution paths, clear separation between analysis and production changes, and a documented approval chain for service-impacting actions.
- Account-support assistants: systems that draft replies or summarize account history require strict role-scoped access to subscriber records and consistent redaction rules for sensitive fields such as call detail elements and identity data.
- Fraud and account-takeover defenses: models that flag SIM-swap risk, subscription fraud, or abnormal usage patterns must support repeatable case review so investigators can justify holds, reversals, or escalations without guesswork.
As AI moves deeper into infrastructure operations, telecom teams need guardrails that prevent cross-subscriber data bleed and restrict automated writes that alter service state. Controls typically focus on scoped permissions for plan changes and suspensions, dual approval for high-impact account actions, and durable records for every system-initiated change that touches billing, identity, or service continuity.
How to build an AI compliance strategy that scales
A scalable compliance strategy relies on two things: a clear mapping from obligations to controls, and an evidence trail that stays consistent across business units and regions. In 2026, that evidence needs to align with sector regulators and with horizontal regimes such as the EU AI Act, which expects structured technical documentation for high-risk uses.
Run a regulatory gap assessment on every AI system
Start by mapping AI usage to the regulatory artifacts each regime expects, then work backward into requirements. For many teams, the gap does not sit in model performance; it sits in missing documentation, unclear accountability, or incomplete operational controls.
A gap assessment should capture the compliance “payload” you must produce per system:
- Regulatory classification and obligation set: EU AI Act category (minimal, limited, high-risk, prohibited); medical device status under FDA SaMD or EU MDR/IVDR where applicable; sector rules such as NERC CIP scope triggers in utilities.
- Required evidence package: technical documentation, validation reports, risk controls, user instructions, and post-release oversight plans that a regulator or examiner can review without ad hoc explanation.
- Data processing boundaries: lawful basis and purpose limitation under GDPR; HIPAA administrative, physical, and technical safeguards for PHI; export-control handling constraints where ITAR applies.
- Vendor assurance needs: SOC 2 reports, contractual retention limits, and audit rights that procurement and compliance teams require before a rollout.
This exercise should produce a prioritized remediation plan: systems with high-risk classifications, safety relevance, or public-facing decision impact first.
Use a risk-based governance framework as the control backbone
Choose a framework, then translate it into a control library that teams can reuse. A framework alone does not scale; standard operating procedures do.
Two practical implementation patterns work well across regulated industries:
- NIST AI RMF as a control taxonomy: align each AI risk type (validity, robustness, privacy, fairness, security) to specific controls—test requirements, documentation templates, and approval steps that match internal audit expectations.
- ISO/IEC 42001 as an operating system: formalize governance processes—policy management, internal reviews, corrective actions, and continuous improvement cycles—so evidence stays consistent across regions and business lines.
This backbone should include a common vocabulary for “what good looks like” across product, legal, security, and risk teams, with minimal reinvention per deployment.
Embed compliance into the AI lifecycle, not as a review step
Lifecycle integration works best when compliance outputs become part of the build itself. Many 2026 requirements hinge on whether an organization can show deliberate design decisions—why a system exists, how it should be used, and where it should not be used.
Build these deliverables into normal delivery workflows:
- Intended-use definitions that constrain deployment: documented scope, contraindications, and operator instructions—especially important when outputs influence clinical, credit, or eligibility decisions.
- Quality and test standards tied to regulated outcomes: acceptance criteria that reflect domain risk, such as clinical safety thresholds or financial control integrity requirements.
- Release documentation that survives scrutiny: technical files, change notes, and validation artifacts that remain complete after urgent fixes, policy updates, or model swaps.
- User-facing transparency assets: clear disclosures for affected individuals when law requires them, plus internal guidance on how staff should interpret and challenge AI outputs.
Treat permissions and integrations as first-class compliance controls
As AI spreads across departments, data pathways proliferate. A scalable strategy needs disciplined integration governance so compliance teams can answer a simple question quickly: what data can flow where, and under what constraints.
Operational controls that reduce cross-system compliance surprises:
- Standard integration reviews: a repeatable checklist for new connectors—data scope, sensitivity classes, retention behavior, and contractual restrictions that apply to each source.
- Access recertification cadence: periodic reviews for high-impact AI access paths—who can use a system, what sources it can query, and what systems it can update.
- Environment separation: clear boundaries between experimentation and regulated production workflows so test activity does not touch restricted datasets or create unmanaged records.
This approach also helps limit tool sprawl: fewer, well-governed integrations beat a long tail of unmanaged ones with inconsistent control strength.
Build continuous monitoring that matches dynamic systems
Compliance teams need evidence that holds over time, not only at launch. Monitoring should support supervisory expectations for post-deployment oversight, especially in high-risk contexts.
A practical monitoring program should include:
- Post-release performance reporting: recurring metrics aligned to the system’s regulated purpose, plus clear thresholds for corrective action when performance shifts.
- Behavioral anomaly detection for AI features: changes in response patterns, retrieval source mix, or workflow outcomes that indicate a hidden dependency change upstream.
- Exception handling records: structured capture of overrides, escalations, and manual corrections so reviews can trace how the organization managed edge cases.
- Incident readiness aligned to regulatory duty: defined internal triggers for security events, safety issues, or rights-impacting errors, with preserved evidence to support disclosure obligations where they exist.
Build an operating model that keeps accountability clear
Compliance breakdowns often trace back to gaps in responsibility. A scalable model assigns ownership for policies, controls, and evidence in a way that matches how work happens.
A durable operating model usually includes:
- Business owners who define acceptable use: clear criteria for what the system may support, what it cannot support, and what review steps are mandatory in sensitive workflows.
- Risk and compliance owners who maintain the control library: consistent templates, testing requirements, and evidence standards across teams and regions.
- Engineering owners who implement controls as defaults: standardized logging, evaluation hooks, and release checks embedded into delivery pipelines.
- Legal and privacy owners who manage external commitments: data processing terms, retention limits, audit rights, and disclosure language consistent with jurisdictional rules.
Training should match role responsibilities: operators need practical playbooks, reviewers need verification standards, and builders need documentation and test expectations that satisfy auditors.
Design for regulatory change and agent-based workflow expansion
Regulatory requirements will continue to evolve, and enforcement timelines will not align across jurisdictions. Flexibility comes from modular governance: a stable baseline plus add-ons for region- or sector-specific obligations.
To prepare for agent-based workflows that execute multi-step tasks, design controls around workflow intent and action boundaries:
- Action classification: separate “draft,” “recommend,” “submit,” and “commit” actions, with policy-defined constraints for each class in regulated processes.
- Evidence continuity across steps: a single record that ties inputs, intermediate decisions, and final outputs to the applicable policy set and system version.
- Approval routing based on impact: dynamic routing to the right reviewer group—clinical oversight, financial control owners, or legal supervisors—based on what the workflow attempts to do.
AI compliance in 2026 isn't a checkbox — it's an ongoing operating discipline that touches every team, workflow, and decision an AI system supports. The organizations that treat governance as a design principle, not a retrofit, will move faster and with more confidence than those still scrambling to catch up.
If you're ready to see how a unified AI platform can help your team work smarter while meeting the compliance demands of your industry, request a demo to explore how we can transform your workplace.