What are the privacy concerns of using customer data in AI?
AI systems depend on customer data to function — and that dependency creates real privacy exposure. Personal information, behavioral patterns, financial records, and health data all feed into models that power everything from personalized recommendations to automated decision-making. The scale at which modern AI collects, processes, and stores this information has outpaced many of the data protection methods organizations still rely on.
The core concern isn't whether organizations use customer data. It's whether they handle it responsibly, transparently, and with safeguards that match the sensitivity of what's at stake. Every AI model trained on real-world customer interactions carries the potential to expose, misuse, or permanently retain information in ways that traditional software never could.
For enterprises in high-trust industries — financial services, life sciences, professional services — the stakes compound quickly. AI-powered experiences like hyper-personalized finance, regulated R&D workflows, and intelligent customer support all increase the volume of sensitive data in motion. That raises the bar for privacy-by-design, compliance readiness, and the kind of architectural discipline that prevents small oversights from turning into major liabilities.
What are the privacy concerns of using customer data in AI?
AI data privacy risks span the full lifecycle of customer information: collection, training, deployment, and ongoing monitoring. Unlike traditional software systems that process data in relatively predictable ways, AI models can memorize rare data points, infer sensitive attributes from seemingly innocuous inputs, and surface personal information through outputs that no one explicitly programmed. The sheer volume of data required to train and fine-tune these systems — often terabytes of text, images, transactions, and behavioral signals — means that sensitive information inevitably enters the pipeline, sometimes without adequate governance in place.
Three categories of risk deserve particular attention from enterprise teams.
Over-collection and purpose creep: Teams building AI systems often gather more customer data than strictly necessary, reasoning that larger datasets improve model performance. This "collect now, figure it out later" approach violates the principle of data minimization and dramatically expands the blast radius if something goes wrong. Equally dangerous is purpose creep — customer data collected for order fulfillment or support interactions quietly repurposed to train a new model, with no updated disclosure or consent. Under frameworks like GDPR, this kind of secondary use without a clear lawful basis creates direct legal exposure.
Transparency gaps and diminished customer control: Once customer data enters an AI pipeline, it becomes difficult for individuals to understand what was used, why, for how long, and with whom it was shared. Data subject rights — access, correction, deletion, objection — grow harder to honor when information is embedded in derived datasets, feature stores, or model weights. A customer who requests erasure under CCPA or GDPR may find that their data persists in ways the organization itself struggles to trace. This opacity erodes trust and complicates compliance at the same time.
Model memorization and extraction vulnerabilities: Research has demonstrated that large language models can inadvertently retain and reproduce verbatim training examples, especially rare or unique strings. Attackers can exploit this through carefully crafted prompts designed to extract sensitive content the model was never intended to reveal. Membership inference attacks — where an adversary determines whether a specific customer's record appeared in the training set — add another layer of risk. These are not theoretical concerns; they represent AI-specific threat vectors that sit outside the scope of conventional cybersecurity defenses.
In industries where AI powers customer-facing personalization or internal knowledge workflows, these risks intensify. A financial services team that deploys AI to analyze transaction patterns for retention and loyalty programs handles data that is both commercially valuable and deeply personal. A life sciences organization that applies AI to research workflows may process patient-adjacent information subject to strict regulatory controls. In both cases, the sensitivity of the data demands more than baseline protections — it requires purpose limitation, strong access controls, and architectural decisions that prevent sensitive information from leaking across system boundaries.
The practical challenge for most enterprises is that AI data privacy risks don't announce themselves. A poorly scoped retrieval query, an insufficiently permissioned search index, or a training dataset that was never audited for sensitive content can each create exposure without any malicious intent. Customer data protection in AI is not a single decision; it's a continuous discipline that must evolve alongside the capabilities of the systems it governs.
How is customer data collected and used in AI systems?
Customer data reaches AI systems through product flows, service operations, and third-party enrichment. That mix creates a “data supply chain” problem: one customer record can pass through many hands, tools, and regions before a model ever uses it.
Where customer data comes from
Enterprises tend to pull customer data from two broad source types, plus a third that often goes undocumented.
- Declared data: Account profiles, web forms, email threads, call center notes, service desk cases, and document uploads such as invoices or identity files. Free-text fields matter most here; customers often include details that no schema expects, such as medical context, payment disputes, or personal addresses.
- Behavioral and device signals: Feature event streams, device and browser attributes, approximate location from network data, and interaction data across integrated apps. On their own these signals can look harmless; once tied to an account or household, they can enable identity inference.
- Purchased or partner data: Data from brokers, affiliates, and risk networks that enrich first-party records. This category creates sharp privacy exposure because provenance and consent terms can remain unclear once the data lands inside internal systems.
How customer data flows through an AI pipeline
Most AI programs reuse the same customer data across multiple purposes: service quality, fraud prevention, product analytics, and model improvement. That reuse makes visibility and control across the pipeline non-negotiable, especially where AI privacy regulations require purpose limitation and demonstrable governance.
A typical pipeline includes these stages:
- Intake and classification: Data moves from operational systems into a shared store or index, then receives tags such as PII, financial, health-adjacent, or child data. Without this step, teams cannot enforce domain-specific rules or restrict high-risk fields.
- Transformation and reduction: Teams apply field removal, token replacement, aggregation, or irreversible masking. Pseudonymization helps, but linkage risk remains; rich behavioral features can re-identify people once combined with other internal datasets.
- Feature and representation build: Systems derive features, embeddings, or summaries that a model can use. These derived artifacts often receive less scrutiny than raw data, yet they can still encode sensitive attributes.
- Model use in production: The application injects customer context into prompts or model inputs to produce classifications, draft responses, or recommendations. A weak boundary between “helpful context” and “excess context” can surface private details in downstream text.
- Quality review and audit evidence: Evaluation sets, human review queues, and system traces store prompts and outputs for troubleshooting and compliance. This layer often outlives its original purpose unless strict retention rules exist.
Risk tends to spike at the handoff between original collection and new model use: teams treat internal reuse as harmless reuse, yet the customer expectation and the legal basis can differ. That gap becomes a data consent in AI problem even when the initial collection looked appropriate.
How operational AI use cases raise the stakes
High-impact enterprise use cases tend to pull the richest context, which also means the highest sensitivity per record.
- Customer service copilots: Agent-assist tools ingest chat transcripts, call summaries, past cases, and internal resolution notes. Poor boundary controls can allow internal commentary or unrelated case history to appear in suggested replies or team-facing summaries.
- Account setup and verification: Identity checks, business verification packets, and exception handling notes can include regulated identifiers. These data types require strict separation from general analytics and short retention windows because exposure risk rises fast.
- Financial services offer optimization: Models that tailor product offers can rely on spend categories, income proxies, merchant patterns, and channel behavior. These attributes can function as sensitive data even when derived rather than explicit, which raises the need for narrow purpose definition, tiered access, and careful controls around derived features.
What are the main AI data privacy risks organizations face?
AI programs shift privacy risk from isolated systems to connected ecosystems: internal teams, external processors, and cross-border infrastructure all touch the same customer records. That shift increases exposure through everyday operations—data copies for testing, vendor handoffs, analytics exports, and long-lived backups.
Sensitive data exposure and leakage
AI can expose sensitive customer data through routine workflows, not just through overt compromise. Support transcripts, identity documents, payment disputes, and health-adjacent notes often sit in the same repositories that feed assistants and analytics, which raises the odds of accidental disclosure through normal outputs.
A few high-frequency leakage paths show up in practice:
- Non-production sprawl: Teams move real customer data into test environments to validate model quality or user experiences; access controls and monitoring often lag behind production standards.
- Re-identification of “de-identified” datasets: Pseudonymized records can snap back to real identities once a dataset contains rich behavioral features or joins with another internal table.
- Operational tooling exposure: Debug traces, monitoring views, and quality review screens can display full-text customer details to broader audiences than intended, especially during incident response and fast fixes.
Unauthorized data collection and use without consent
Data intake can drift into gray areas fast—especially when AI initiatives pull from sources that feel “available” rather than sources that match customer expectations and documented permissions. Public or semi-public content, partner feeds, and tracking-derived signals can enter a model pipeline without a clear story about notice, consent, and downstream use.
Common consent failures include:
- Implicit collection defaults: Opt-out settings, pre-checked boxes, and silent feature enablement can conflict with the level of agency customers expect for AI use.
- Downstream reuse through third parties: Annotation vendors, model hosting providers, and analytics platforms can become accidental channels for secondary use unless contracts and controls enforce strict purpose limits.
- Use beyond the original promise: Data captured for service delivery can later support profiling, segmentation, or automated decisions, which can violate data consent in AI expectations even when the initial intake looked compliant.
Data breach implications in AI environments
AI environments often aggregate high-value datasets and new access paths, which creates attractive targets for attackers and new failure modes for defenders. Traditional security controls still matter, but AI introduces novel ways to trigger data disclosure through the model interface itself.
Threat vectors that deserve explicit coverage in an AI security program:
- Prompt injection attacks: Malicious instructions hidden inside content can override policy boundaries and coerce the system to reveal restricted information or perform unintended actions.
- Model inversion: Carefully chosen queries can expose sensitive attributes that the model learned from data patterns, even without direct access to the underlying records.
- Data reconstruction via repeated queries: An attacker can iteratively probe the system to recover fragments of proprietary or personal information, especially when the system returns overly detailed outputs or rich confidence signals.
Practical frameworks emphasize three layers at once: governance with clear ownership and allowed data classes; technical controls such as segmented access, encryption, and output filtering; continuous testing that targets LLM-specific weaknesses with red-team exercises and adversarial prompts.
Bias and AI surveillance concerns
Customer data often mirrors unequal outcomes—disparate access to services, uneven enforcement, and biased historical decisions. When AI systems learn from that history, they can reproduce the same inequities at scale through automated scoring, eligibility decisions, identity checks, and prioritization logic.
Surveillance risk rises when AI expands the use of behavioral monitoring beyond what customers understand or accept. Persistent tracking across devices, channels, and time can cross from service optimization into intrusive profiling—especially in sensitive domains such as health, employment, education, personal finance, and services used by children, where even lawful processing can cause disproportionate harm.
What regulations govern customer data use in AI?
Most privacy law does not carve out a special rulebook for “AI.” It sets requirements for personal data, then holds AI features to the same standards—plus extra duties where automated systems raise risk, opacity, or scale. That combination pushes enterprises toward formal governance artifacts: assessments, contracts, technical documentation, and evidence that controls work as intended.
The current landscape blends long-standing privacy statutes with newer AI-specific rules. The practical implication: compliance work must cover both the data layer and the system layer, with documentation that can survive audits across regions.
GDPR: accountability, assessments, and enforceable processor controls
GDPR compliance for AI depends as much on operational discipline as on policy language. Regulators expect proof—records that show what data exists, who touches it, and which safeguards apply across each system that uses personal data.
Areas that most often drive concrete requirements for AI programs include:
- Accountability documentation: Records of processing activities (Article 30) and internal control evidence that ties a dataset to an approved use case, a responsible owner, and a defined set of safeguards.
- Impact assessment triggers: Data Protection Impact Assessments (Article 35) for high-risk processing, with documented mitigations and residual risk evaluation that reflect real system behavior rather than generic templates.
- Controller–processor obligations: Data Processing Agreements (Article 28) that constrain vendor use, subprocessor access, security measures, and audit rights—especially for model APIs, annotation services, and managed platforms.
- Security expectations with breach duties: Appropriate technical and organizational measures (Article 32), plus breach notification duties (Articles 33–34) that require fast visibility into what data exposure occurred and which individuals face risk.
EU AI Act: system governance for high-risk use, plus obligations for certain model providers
The EU AI Act adds AI-specific duties that sit alongside GDPR. It focuses on how an AI system behaves in real use—risk controls, transparency, traceability, and structured oversight for specific categories of AI.
For high-risk systems, the Act introduces requirements that resemble regulated product disciplines:
- Risk management and quality management systems: Defined processes that govern design changes, testing protocols, and control ownership over time.
- Conformity assessment and technical files: Pre-deployment evidence that the system meets required standards, with documentation sufficient for regulator review.
- Event logging and post-market oversight: Logs that support incident analysis and post-deployment monitoring, plus processes for issue detection and corrective action.
The Act also includes targeted restrictions for certain practices, such as large-scale facial image scraping for biometric databases, which can affect data sourcing decisions well upstream of model development.
United States: state privacy statutes, plus enforcement pressure from consumer protection authorities
In the U.S., state privacy laws define consumer rights and business duties that apply to AI features when they rely on personal data. CPRA in California, plus laws in states such as Colorado and Virginia, create obligations around notice, access, deletion, and special handling for sensitive data, with requirements that vary by jurisdiction.
Outside state statutes, consumer protection authorities add a second axis of risk. The Federal Trade Commission has emphasized truthfulness, fairness, and equity in automated systems; enforcement can follow where companies make privacy promises that do not match real data use or where data practices cause consumer harm. Federal policy guidance such as the White House Blueprint for an AI Bill of Rights also shapes expectations for data privacy and user control in enterprise governance, procurement, and audit criteria.
Cross-jurisdiction reality: adaptable compliance becomes a core capability
Multinational operations must accommodate differences in legal definitions, notice standards, and enforcement posture without fragmenting controls by region. That demands a compliance framework that can absorb change—versioned policies, standardized vendor terms, consistent data classification, and audit-ready evidence that maps controls to each jurisdiction’s requirements.
Sector obligations can exceed general privacy law. In life sciences and other regulated environments, audit standards often require detailed documentation, strict access governance, and clear change control for systems that touch regulated datasets or patient-adjacent context.
What ethical considerations apply to customer data in AI?
Ethics starts where statutes stop. Regulations can demand specific disclosures, security measures, and paperwork; ethical practice demands restraint and care when customer data shapes outcomes that affect real lives.
An AI feature can follow the letter of the law and still violate customer expectations. Ethical AI data use sets guardrails for what feels fair, what feels intrusive, and what deserves human oversight—especially when automated output influences pricing, access to service levels, or account treatment.
Fairness and proportionality in AI-driven outcomes
Customer datasets often reflect uneven service, inconsistent enforcement, and past business choices that did not treat every group the same way. A model that optimizes conversion or cost can amplify those patterns unless teams define fairness goals and verify performance across populations.
A practical ethical standard includes:
- Fairness checks that focus on real-world impact: Teams should compare error rates and adverse outcomes across groups, then review the specific scenarios that drive harm for smaller segments.
- Data-to-benefit justification: Each customer attribute should link to a clear customer benefit in the specific feature; extra fields that improve model accuracy marginally can impose outsized privacy cost.
- A path to challenge outcomes: High-stakes use should include human review options, clear correction steps, and documented rules that prevent staff from treating model output as a final decision.
Transparency that people can act on
Most customers cannot make meaningful choices from broad, legalistic statements. Ethical transparency requires plain explanations that describe which data classes influence an outcome, which factors do not, and what control a customer can exercise in that context.
Ethical transparency tends to require:
- Plain-language reasons with clear boundaries: A short rationale should separate verified account facts from statistical inference, so customers understand what the system “knows” versus what it “predicts.”
- Choice at the right moment: Controls should appear where data enters the feature or where a decision appears, not only inside a general privacy policy.
- Respect for opt-out signals where feasible: Mechanisms such as Global Privacy Control and platform-level permission prompts (for example, App Tracking Transparency on iOS) set a higher bar for customer agency; ethical design should honor the spirit of those signals even when the law does not force strict adoption.
Sensitive domains and heightened duty of care
Certain data types carry higher harm potential regardless of formal legality. Medical details, precise location, biometric identifiers, payment card details, data about minors, and employment history can create lasting damage through exposure, inference, or misuse.
Ethical handling in these domains usually includes stricter internal rules than baseline compliance requires:
- Hard limits on specific inferences: Teams should ban certain derived traits outright, such as medical status proxies from purchase histories or life-event guesses from location traces.
- Stronger defaults for internal visibility and data lifespan: Narrow role scopes and enforced purge deadlines should apply to the most sensitive fields and to any derived artifacts that encode them.
- No silent escalation of customer communications: A support transcript should not feed a risk score or segmentation label without explicit internal review standards and a clear customer-facing explanation that matches the impact of that use.
Accountability across the full end-to-end data path
AI programs distribute responsibility across product, data, security, legal, and external processors. Ethical accountability requires named owners for high-impact use cases, plus disciplined control over data handoffs, derived datasets, and service-provider access.
A workable accountability model includes:
- Clear boundaries between advice and action: Teams should document when staff may rely on model output and when they must override it, with examples that reflect real operational edge cases.
- Human judgment at defined checkpoints: Review gates should exist for ambiguous cases and for decisions that can materially affect a customer, with escalation routes that staff can use without friction.
- Contract and control expectations for outside processors: Agreements should prohibit out-of-scope reuse, require strict deletion timelines, and demand evidence of safeguards for any environment that handles customer data.
How can organizations protect customer data in AI systems?
Customer data protection in AI depends on control points that sit close to the data itself: identity, access, context assembly, and downstream storage. Privacy teams can no longer rely on policy documents alone; they need enforceable rules inside pipelines and user experiences.
The strongest programs treat AI as a data supply chain. Each handoff—collection, enrichment, labeling, feature creation, vendor processing, and production use—gets a defined owner, a bounded purpose, and a control that produces evidence.
Implement permissions-aware architecture from the start
Permissions-aware design should not stop at “user can see document X.” It must cover data slices inside the document, derived fields, and any system that constructs context for an AI response.
Key patterns that reduce unauthorized exposure:
- Central policy decision point: One service evaluates entitlements across apps and data stores, then issues short-lived access grants; every AI request depends on that grant, not on static API keys.
- Attribute-based access control (ABAC): Policies reference attributes such as region, contract tier, case assignment, and data class (PII, financial, health-adjacent). This approach prevents overbroad access that role-based access control often allows.
- Context assembly rules: A dedicated layer selects input snippets based on sensitivity tags and need-to-know; it excludes entire categories by default (identity artifacts, payment details, child data) unless a feature explicitly requires them.
Limit data collection and enforce retention policies
A privacy-first AI pipeline starts with strict intake discipline. Data minimization must translate into code-level allowlists and time-bounded storage, not best-effort habits.
Controls that hold up under fast iteration:
- Schema allowlists at ingestion: Pipelines accept only approved fields per use case; any new field triggers a review path before it enters shared stores.
- Quarantine for high-risk payloads: Free-text sources such as emails and transcripts route through a staging zone that strips or redacts sensitive strings before any downstream use.
- Retention schedules tied to data class: Each dataset receives a retention window aligned to its purpose; automated deletion applies to raw records, derived tables, and support artifacts such as debug traces.
Conduct ongoing privacy risk assessments
AI risk changes with every new dataset, connector, and prompt template. A structured assessment cadence keeps controls aligned to real behavior, not only to design intent.
A practical assessment approach:
- Lifecycle checkpoints per release: Product, security, legal, and data owners approve changes that affect data classes, vendor processing, or decision impact; the review records assumptions and boundaries.
- Disclosure risk exercises: Teams run scripted attempts that target sensitive detail disclosure in outputs, cross-user data exposure, and policy bypass through malicious inputs embedded in customer content.
- Quality and fairness validation: Evaluation sets include edge cases that reflect vulnerable populations and high-impact decisions; the process documents failure modes and mitigation plans.
Build encryption, anonymization, and access controls into AI workflows
Privacy controls need technical depth because AI pipelines replicate data. Protection should persist even when a dataset moves into analytics, evaluation, or vendor processing.
High-leverage safeguards:
- Confidential processing for sensitive workloads: Hardware-backed isolation (confidential compute) reduces exposure during model calls and data transforms in shared cloud environments.
- Deterministic redaction with a separate secret store: Systems replace high-risk identifiers with consistent placeholders; the mapping stays in a vault with separate access rules and separate audit controls.
- Data loss prevention for prompts and outputs: Inline inspection blocks or transforms content that matches regulated patterns (account numbers, national IDs, medical identifiers) before it reaches a model endpoint or a user interface.
Maintain audit trails and reporting transparency
Audit readiness requires more than event capture. It requires an evidence chain that connects an AI output to the exact inputs, policies, and authorizations that allowed the system to use customer data in that moment.
Evidence that supports AI compliance issues:
- Lineage records for data and models: Each model version links to its approved data sources, transformations, and evaluation results; change control shows what changed and who approved it.
- Vendor and subprocessor registers: Contracts, retention terms, and processing locations stay current; records show which providers handle which data classes and under which safeguards.
- Customer-facing reporting that reflects real controls: Disclosures describe data categories in use, purposes, retention windows, and third-party processing in clear terms that match the system’s actual behavior.
How to build a privacy-first AI strategy that scales
A privacy-first AI strategy scales when it treats customer data as a regulated supply chain, not a pile of useful inputs. Every new model feature creates new paths for inference, extraction, and unintended disclosure, so the strategy must hold under continuous change.
Scale also demands repeatability. Teams need a way to ship new use cases without a new, bespoke privacy debate each time—while still meeting the expectations that regulators and customers now place on AI systems.
Establish privacy as a design principle, not a constraint
A scalable program starts with design-time requirements that engineers can implement and test, not broad principles that only live in policy decks.
- Define “allowed data” in terms of harm, not convenience: Treat high-impact domains (health, finance, children, employment) as higher duty-of-care zones; require explicit justification for any use that touches them, even when the data looks “operational.”
- Set model behavior requirements, not only data requirements: Add non-negotiables such as “no reproduction of unique identifiers,” “no disclosure of third-party personal data,” and “no output that reveals training set membership.” These constraints reflect known LLM failure modes such as memorization and extraction.
- Standardize privacy acceptance tests: Create reusable tests that probe for data extraction, attribute inference, and leakage through free-text inputs. OWASP-style prompt injection and “training data recall” tests should run like any other pre-release quality gate.
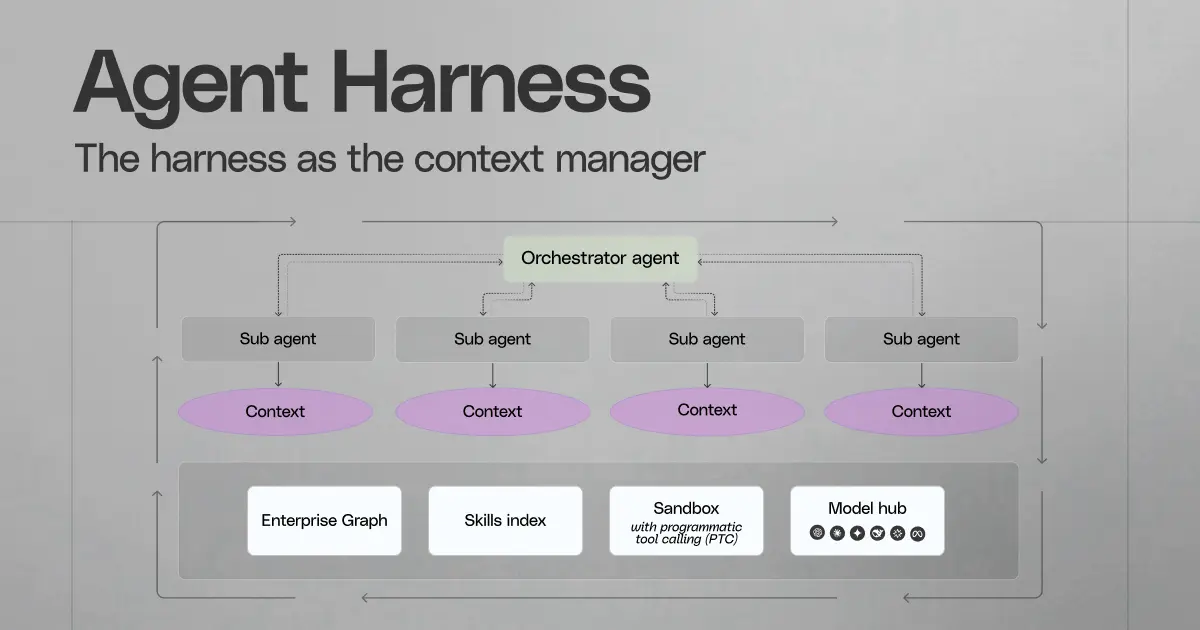
Unify governance across every AI touchpoint
Governance fails at scale when each team invents its own rules for datasets, model access, and evaluation. One shared operating model keeps AI privacy consistent across chat interfaces, embedded product features, workflow automation, and agent toolchains.
- Use policy-as-code for AI rules: Translate privacy policies into machine-enforceable controls that sit inside pipelines and deployment tooling, not only in documentation.
- Adopt standardized AI documentation artifacts: Maintain system cards and model cards that describe intended use, disallowed use, data sources, evaluation limits, and known failure modes. These artifacts make review faster and reduce ambiguity during audits.
- Treat vendors as part of the data boundary: Maintain a clear map of which providers touch which customer data classes, where processing occurs, and which contractual controls prevent retention or reuse. This supports the accountability expectations that show up across data protection authorities.
Invest in infrastructure that enforces real-time permissions and boundaries
Infrastructure should reduce privacy reliance on human judgment during incident response, rapid iteration, and broad rollout. AI introduces new risks at runtime—prompt injection, data exfiltration through outputs, and inference from repeated queries—so boundaries must hold under adversarial conditions.
- Runtime isolation for sensitive inference: Use hardened execution paths for the most sensitive workloads—network egress controls, confidential compute where appropriate, and strict separation between inference systems and general analytics environments.
- Rate limits and anomaly detection for extraction patterns: Monitor for repetitive probing that resembles membership inference or content reconstruction attempts; throttle and alert when query patterns match known extraction behaviors.
- Output risk controls as a first-class feature: Apply structured output rules for sensitive workflows—redaction for regulated identifiers, refusal for prohibited requests, and constrained templates for high-impact communications such as denial notices or account restrictions.
Create cross-functional accountability that matches technical reality
Privacy outcomes depend on coordinated decisions across product, engineering, security, legal, and operations—plus external processors who handle data during labeling, hosting, or support. A scalable model assigns clear ownership for decisions that shape both data exposure and customer impact.
- Single owner per AI capability, plus a standing review group: One accountable owner makes day-to-day calls; a cross-functional group sets shared thresholds for risk and approves exceptions that affect sensitive categories or high-impact decisions.
- Operational playbooks for privacy incidents: Define incident paths for AI-specific failure modes—prompt injection, unintended disclosure in outputs, vendor processing drift, and over-collection discovered after launch.
- Decision records that capture tradeoffs: Keep short, durable records that explain why a data class entered a use case, what mitigations exist, and what evidence supports the decision. This supports regulatory expectations for demonstrable accountability.
Validate strategy in the deployments that move fastest
The best proof of privacy-by-design shows up in real deployments with messy text, high volume, and constant iteration. Customer support assistance and retention personalization often stress systems first because they rely on rich context and fast release cycles.
Validation should focus on measurable properties that map to research-backed risks:
- Leakage probes against real prompts and content: Test with adversarial inputs that mimic customer-provided text, including hidden instructions and sensitive strings that can trigger prompt injection or disclosure.
- Inference resilience checks: Evaluate whether outputs allow attribute inference or membership inference under repeated querying, especially where the system reveals confidence signals or overly specific details.
- Third-party processing verification: Confirm that service providers honor data handling terms in practice—no unapproved retention, no reuse outside scope, and clear deletion behavior across support and debugging workflows.
Treat audit readiness as a scaling requirement in regulated environments
Highly regulated environments require evidence that systems stay within declared purpose, maintain appropriate safeguards, and support oversight. AI adds complexity because outputs can vary, models can change, and data can propagate across derived artifacts and vendor systems.
Audit readiness should include:
- Provenance for models, datasets, and evaluations: Maintain traceable records that link each production release to its approved data sources, risk assessments, and evaluation results, with enough detail to reproduce key checks.
- Tamper-evident event records for sensitive access: Use immutable logs for access to high-risk datasets and for execution of high-impact AI actions, so investigations and audits rely on trustworthy evidence.
- Regulatory mapping that stays current: Maintain a living matrix that maps controls to obligations across GDPR, state privacy laws, and EU AI Act requirements for high-risk systems, including oversight processes and transparency commitments.
Privacy isn't a checkbox you clear once — it's an ongoing discipline that evolves alongside every new model, dataset, and use case your organization deploys. The organizations that get this right treat customer data protection as a core capability, not a compliance afterthought, and they build systems that earn trust by design.
We built our platform to help enterprises move fast without compromising on the privacy, permissions, and governance their customers expect. Request a demo to explore how we can help AI transform your workplace — with the safeguards that make it sustainable.