What is metadata classification and why it matters for security
Organizations generate vast amounts of data every second, yet much of the security context for that data remains hidden in a layer most people never see — metadata. This invisible substrate captures who created a file, when it was last modified, where it lives, and who has permission to access it, forming a rich but often overlooked foundation for enterprise security.
The challenge extends beyond simple awareness. Structured approaches to metadata are essential for enterprises that need to protect sensitive information, maintain compliance, and support AI-driven workflows — all at scale. Yet only 27% of organizations can track more than 75% of their sensitive data across enterprise environments, and 82% of cybersecurity professionals report gaps in finding and classifying organizational data across production systems.
Metadata classification bridges the gap between data chaos and security control. By applying systematic categorization to metadata attributes, organizations can automate policy enforcement, detect anomalies faster, and ensure that every piece of information carries the context needed to protect it throughout its lifecycle.
What is metadata classification?
Metadata is often described as "data about data" — the descriptive layer that captures attributes like authorship, creation date, file type, storage location, and access permissions for every digital asset an organization manages. Every email, document, database record, and collaboration thread generates metadata, and in aggregate, these attributes form a detailed map of how information flows across the enterprise.
Metadata classification is the practice of systematically categorizing these attributes so they become actionable. Rather than letting metadata exist as raw, unstructured descriptors scattered across hundreds of applications, classification assigns sensitivity levels, maps ownership, and tags data with labels that drive downstream security and governance decisions. The distinction matters: unclassified metadata is like a library with millions of books but no catalog, titles, or shelf labels. Classified metadata transforms that same library into a system where every asset is identifiable, searchable, and protectable.
In practice, classification works by applying a defined taxonomy — a consistent set of categories and labels — to metadata attributes across the enterprise data landscape. A sensitivity label such as "Confidential" or "PII" attached to a document's metadata can automatically trigger encryption, restrict sharing, or enforce access controls without any manual intervention. Ownership tags ensure accountability. Retention labels govern how long data persists and when it should be archived or deleted. These classifications are not static; modern approaches use automated classifiers and machine learning models that continuously crawl and tag content, achieving 80% or higher accuracy in distinguishing truly sensitive data from benign noise. This automation is critical for enterprises dealing with large and growing volumes of unstructured data — manual classification simply does not scale.
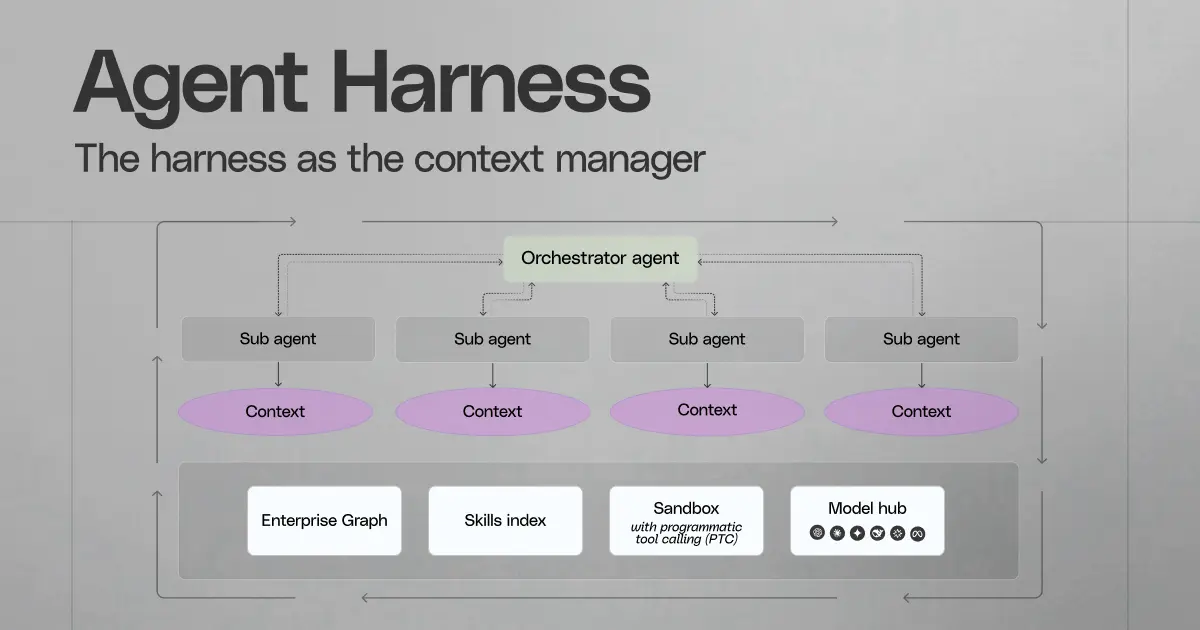
The importance of metadata classification compounds in environments where AI-powered tools retrieve and surface information across the enterprise. When an employee asks an AI assistant a question, the system must respect what that user is authorized to access. Metadata classification, tightly coupled to permission structures, ensures that retrieval honors those boundaries — preventing sensitive content from appearing in results where it does not belong. Without this foundation, even the most sophisticated AI platform risks surfacing unauthorized information or producing results grounded in data the user should never have seen.
Types of metadata that matter for security
Each metadata type serves a different security purpose: one helps teams pinpoint what an asset represents, another expresses control intent, another exposes shape and dependencies, another reveals technical fingerprints, and another preserves evidentiary trace.
Descriptive metadata
Descriptive metadata captures identifiers that help people and systems recognize content across tools that store the same facts in different forms. In practice, this metadata type supports fast correlation across incidents, audits, and investigations—especially when content copies spread across chat, email, drives, and ticketing systems.
High-value descriptive fields:- Titles, subjects, and headings: strong signals for rapid triage when a dataset or document set relates to regulated topics (payroll, benefits, customer exports) or internal initiatives.- Authors and editors: attribution support when an asset appears outside its expected workflow; author fields often persist across exports and format conversions.- Keywords and tags: controlled tags help reduce false positives in monitoring; free-form tags expose sensitive project names and codenames that never appear in official templates.
Administrative metadata
Administrative metadata describes the access model and management state for an asset: entitlements, ownership, sharing posture, and change history. This metadata type powers access reviews, exposure reduction, and policy validation because it shows how a system treats the asset, not just what the asset contains.
Key administrative elements with direct security impact:- Entitlements and share scope: explicit ACLs, inherited access, public-link status, and external collaborator flags; these fields surface overshare conditions that content inspection misses.- Owner and steward records: accountable identities for remediation workflows; security teams need a clear escalation target for revocation, relabel, or migration.- Access and permission change audit events: a reliable record of entitlement drift over time; these logs support root-cause analysis after exposure and prove control operation during audits.- Sensitivity labels as portable handling intent: products such as Microsoft Purview sensitivity labels store classification as metadata that can travel with the document, which helps policy interpretation stay consistent across apps and exports.
Structural metadata
Structural metadata defines how parts relate: schema, hierarchy, and embedded components. Security value often comes from invariants—critical systems and file formats tend to look the same day to day, so structural deviation can signal tamper, evasion, or unauthorized change.
Structural signals that deserve attention:- Schema and relationship shifts: new tables, renamed columns, altered constraints, or unexpected joins; these changes can introduce new exposure paths or break downstream controls.- Embedded objects and active content containers: macros, linked objects, and nested archives; structural complexity correlates with higher inspection and sandbox need.- Type/structure mismatch: a file that claims one format yet carries headers or internal structure that aligns with another; this pattern often supports bypass attempts.
Technical metadata
Technical metadata captures system-level attributes that support detection, forensics, and privacy controls. This layer often leaks context users never intend to share, which makes it a high-priority target for sanitization in external distribution workflows.
Technical attributes with recurring security value:- Format, encoding, and compression details: uncommon encodings, repeated archive nesting, or suspiciously uniform file sizes can indicate obfuscation or covert transfer.- Device and software fingerprints: “created with” fields, device models, and application versions can expose internal toolchains and patch posture.- Image EXIF fields: GPS coordinates and device identifiers can reveal employee location patterns and sensitive facility geography.- Cloud instance metadata services context: in modern cloud environments, metadata services such as instance metadata endpoints can become a credential-theft path during SSRF campaigns; security teams should treat exposure of these metadata channels as a high-severity control failure, not a minor misconfiguration.
Provenance metadata
Provenance metadata preserves lineage and custody across systems: origin, transformations, and the sequence of handlers. This record becomes essential when security teams need defensible answers that hold up under legal review or regulatory inquiry.
Provenance support tends to show up in three places:- Forensic timelines with chain of custody: clear proof of who touched an asset, which systems processed it, and what transformations occurred.- Data lineage for derived outputs: trace from report or dashboard back to upstream sources and transformation steps, which helps validate impact scope after an incident.- AI governance traceability: an auditable record of the source set and transformation path that influenced an AI-produced response, plus proof that the retrieval route stayed within policy.
KB validation/enrichment:- Administrative metadata parity across sources: permission and share-state fidelity across indexing, search, and AI experiences prevents silent entitlement mismatches; this pattern shows up in platforms such as Glean.- Provenance as an audit primitive: lineage records make post-incident reviews and AI governance reviews possible without reliance on manual reconstruction.
How does metadata classification enhance data security?
Metadata becomes a security control once it carries consistent meaning across systems. Classification supplies that shared meaning—so policies, monitoring, and governance workflows can operate on a stable set of attributes instead of ad hoc file locations or team conventions.
This shift matters most in large environments with many repositories, fast content churn, and mixed structured and unstructured data. Classification turns “security context” into an input that tools can enforce, measure, and audit without constant manual interpretation.
Policy enforcement that scales across tools
Classification strengthens enforcement by standardizing how security intent travels with information, even as that information moves across apps, exports, and formats. Instead of hand-built exceptions per repository, teams can express controls in terms of attributes: sensitivity, business domain, jurisdiction, owner, record category.
Practical enforcement patterns that depend on classified metadata:- Attribute-based access decisions: policies evaluate sensitivity, role, and business need at request time; high-sensitivity assets require tighter conditional access (managed device, strong auth, approved network).- Jurisdiction and residency controls: regional tags (EU, UK, US state-level) guide where data can store, which sharing paths remain allowed, and which processors can handle it.- Retention and legal hold alignment: lifecycle tags drive preservation, deletion, and hold behavior with less ambiguity—especially when the same content exists in multiple systems.- Security ticket reduction through standard handling: consistent labels reduce “one-off” reviews by making default handling rules clear for common data types (contracts, employee records, customer exports).
Better detection through baselines and metadata signals
Classification makes detection more actionable because it links activity to impact. A single alert about a download spike means little; the same spike tied to assets classified as regulated or highly sensitive changes priority, triage order, and response workflow.
Where classified metadata improves signal quality:- Impact-weighted alerting: events that touch regulated classes (PII, financial, health) receive higher severity, shorter SLA, and broader stakeholder visibility.- Faster incident scoping: ownership, system-of-record tags, and timestamps help responders map exposure scope, identify authoritative copies, and reduce time spent chasing duplicates.- Privacy-aware investigation: metadata often supports threat hunting without full content access, which limits data exposure during investigations and supports internal privacy commitments.
Research in the space commonly reports large gains when teams operationalize metadata analytics—up to a 60% improvement in threat detection effectiveness—with meaningful reductions in time-to-triage once alerts include well-classified context.
Stronger AI security through permission- and label-aware retrieval
Classification helps AI governance in ways that go beyond “what appears in results.” It enables policy-driven decisions about which model modes, tools, and data-handling pathways remain acceptable for a given task and data class.
Controls that rely on robust classification when teams deploy LLM-based tools:- Processing-mode routing: sensitive classes trigger stricter handling modes—no external processing, no long-lived logs, and tighter controls on intermediate artifacts such as drafts and exports.- Tool gating by data class: the system can disable higher-risk tools (auto-share, auto-email, bulk export) when the working set includes regulated or high-impact data.- Output constraints and redaction: response rules vary by label—shorter excerpts, masked identifiers, or required structured summaries for regulated categories.- Demonstrable governance for audits: in regimes such as GDPR—where metadata itself can qualify as personal data—classification helps prove that AI workflows follow retention limits, access rules, and approved processing purposes.
What are the risks of poor metadata classification?
Poor metadata classification creates a gap between what the organization stores and what security controls can reliably protect. When key attributes—data class, business context, accountable party, and exposure state—lack consistent labels, enforcement shifts from policy to judgment, and exposure windows expand across every system that holds a copy.
The operational cost shows up fast: many enterprises leave the majority of enterprise data outside meaningful analysis, with research that places that figure at roughly two-thirds. That deficit leaves security teams with alerts and access reviews that lack context, which slows prioritization, triage, and proof of control effectiveness.
Security blind spots that lead to silent exposure
Misclassified or unclassified metadata breaks the control loop that keeps sensitive content within defined boundaries. The most common failure modes can look routine until an incident forces deeper inspection.
- No accountable custodian at scale: missing custodian or business-owner fields block remediation; security teams lack a clear escalation route for access correction, relabel, or disposal.
- Unknown exposure state: absent or inconsistent exposure markers hide broad link access, external guest access, and permissive group grants; risky assets can persist in plain sight.
- Access creep without traceability: incremental privilege expansions over months or years can leave sensitive assets open to far more users than intended, with no dependable record for root-cause analysis.
- Untracked duplication across workflows: copies spread through project hubs, knowledge bases, CRM attachments, and exported reports; without consistent labels, each copy becomes its own unmanaged risk.
Metadata as a privacy payload
Metadata can carry sensitive context even when content stays encrypted or otherwise protected. Recipient networks, meeting attendance lists, device identifiers, and timestamp patterns can expose relationships and routines that qualify as personal data under many privacy regimes.
Breach analysis has repeatedly shown that “only metadata” still supports high-impact inference—who communicated with whom, which teams collaborated, which customers received attention, and how work moved through the organization. That dynamic creates a second protection target: not just the content itself, but the surrounding attributes that make it identifiable and linkable.
Reactive compliance and weak audit posture
Audits rarely fail because a policy does not exist; they fail because evidence lacks continuity across systems. Poor classification undermines the ability to demonstrate consistent handling, especially when retention, residency, and access obligations differ by data class.
Common audit and compliance breakdowns:- Unmapped obligations to assets: access records exist, yet no reliable data class or accountability tag ties events to a specific control requirement.
- Inconsistent lifecycle proof: record category and retention attributes vary by repository, which weakens evidence for preservation, disposal, and legal hold actions.
- Ambiguous purpose and scope: without consistent context tags (business domain, customer impact, regulated category), compliance reviews turn into manual reconstruction efforts.
AI exposure from inconsistent labels and permissions
Enterprise AI experiences amplify classification errors because answers often depend on rapid context assembly across many repositories. A single incorrect label, outdated access signal, or missing lineage attribute can route sensitive sources into a broader audience context, or create outputs that security teams cannot defend after the fact.
Risk concentrates in three areas:- Cross-audience source inclusion: weak access signals and inconsistent labels can allow an AI system to draw from sources outside the intended audience boundary.
- Low traceability for outputs: missing lineage fields can block validation of which sources influenced an answer, which weakens governance review and incident response.
- Overpermissive handling defaults: absent labels can trigger “standard” handling modes that fit low-risk content, even when the asset belongs in a restricted class.
Security programs that rely on occasional spot checks struggle here. Modern environments require continuous review across many sources plus rapid detection of overshared or mislabeled assets to reduce exposure time and prevent drift.
The role of metadata classification in data governance and compliance
Metadata classification supports governance because many regulations treat metadata as regulated data in its own right. GDPR, for example, can treat email headers, access records, and other metadata as personal data; regulators can evaluate how long an organization keeps that metadata and who can access it.
This matters across security, privacy, and records programs. A consistent taxonomy for information types and handling labels lets teams align policy language with the way systems store files, messages, database exports, and logs.
Evidence that stands up in audits
Auditors need clarity on what data classes exist, which controls apply, and how systems map to those expectations. Metadata classification provides a durable vocabulary that security, privacy, IT, and legal teams can share.
- Security categorization aligned to standards: Labels can reflect structured categorization models such as NIST SP 800-60 (information types and impact levels), which supports consistent control selection across business units.
- Unambiguous scope definition: Classification tags reduce ambiguity in audit sampling because reviewers can select assets by class (PII, financial, health) instead of file location or team name, which often shifts over time.
- Control testing with measurable coverage: Coverage metrics—percent labeled, percent unlabeled, and exception counts by system—support repeatable testing without reliance on ad hoc interviews.
Lineage and chain of custody for regulated data
Regulated workflows often require proof that a record set stays intact from creation through disclosure—especially for eDiscovery, breach notification support, and regulated reporting. Metadata classification complements this by standardizing identifiers and integrity signals that help teams reproduce what a recipient or regulator saw at a specific point in time.
Lineage-grade evidence often depends on metadata that stays stable across repositories:
- Version identity and integrity markers: Immutable timestamps, cryptographic hashes, and digital signatures help establish that a produced artifact matches an internal version.
- Authoritative source declarations: System-of-record and record-series tags clarify which repository holds the controlling copy, which reduces conflicts between duplicates.
- Reproducible export context: Metadata that records export method, filter criteria, and transformation tool version supports defensible reproduction without manual reconstruction.
Retention, disposal, and cross-border compliance
Governance programs often overlook the fact that metadata itself has its own lifecycle. Email metadata retention, security telemetry, and collaboration audit metadata can fall under privacy rules; a recent European enforcement action set a clear retention benchmark for email metadata, which signals regulator attention on this layer.
Cross-border obligations also extend to metadata stores, especially when centralized logging or analytics platforms move operational data across regions.
- Metadata minimization by default: Field-level controls can limit collection to what policy requires; EXIF removal for images and selective header retention reduce unnecessary exposure.
- Regional controls for operational metadata: Residency rules should cover logs, audit metadata, and identity context—not only content repositories—because these datasets can reveal behavior patterns and relationships.
- Disposition verification beyond the primary copy: Deletion workflows should account for derivative stores such as indexes, caches, and exported reports that can persist after content removal.
How metadata classification supports the data lifecycle
Metadata classification must cover more than documents and database rows; it must also cover the metadata exhaust that work systems produce by default—email headers, access logs, file properties, and device artifacts. That exhaust often carries sensitive context on its own, so lifecycle controls need to treat metadata as a first-class asset with its own exposure surface.
A lifecycle-aware program ties classification to the events that change metadata shape and meaning—file conversions, export workflows, sharing to external parties, and ingestion into security telemetry. That approach keeps security context useful across collaboration tools, identity systems, and monitoring stacks without reliance on manual cleanup.
Creation: capture context before it disperses
Creation events generate more metadata than most teams expect: author identity, tenant and domain identifiers, application “created by” fields, and default sharing posture. Early classification can attach guardrails to that metadata layer before it travels with the asset into downstream systems.
Creation-stage controls that reduce long-term friction:- Field-level metadata capture standards: a fixed set of required attributes (owner, business unit, data type, intended audience) that stays consistent across file stores, ticketing tools, and CRM attachments.
- Automatic classification for “metadata-only sensitive” cases: categories that flag risk even when content stays benign—examples include customer lists in subject lines, project codenames in titles, or location fields inside image EXIF.
- Source system fingerprints as part of classification: the system of origin and authoring tool version can signal risk class—especially for exports from finance and HR systems that often include regulated data by default.
Active use: keep classification aligned to collaboration mechanics
Day-to-day work triggers repeated metadata mutation: PDF export from a doc, copy into a new folder, reply-all email chains, and attachment reuse across tickets. Classification supports this phase when it tracks the collaboration mechanics themselves—share scope changes, external recipient introduction, and rapid cross-app propagation.
Operational patterns that work well during active use:- Outbound metadata hygiene rules: policy-driven removal or masking of fields that leak context—EXIF GPS data, internal file paths, author usernames, and hidden revision history that can survive format conversion.
- Metadata access segmentation: separate permissions for content and for high-sensitivity metadata such as audit events, access logs, and identity attributes; this limits lateral visibility into who accessed what.
- High-risk channel tagging: explicit classification for distribution methods that raise exposure odds—public links, external guests, bulk export actions, and attachment forwarding outside managed mail domains.
Archival and disposal: control the afterlife of metadata
Archived material often shifts from “work artifact” to “evidence artifact,” which changes who needs access and what must stay intact. Disposal also applies to metadata stores—telemetry pipelines, access logs, and system-generated headers—which can persist long after the associated content disappears.
Controls that reduce lifecycle residue:- Metadata minimization at rest: storage rules that keep only the fields required for audit, security, and operational needs; discard or tokenize fields that add privacy risk without security value.
- Separation of archival classes: distinct classification for records, drafts, and transitory collaboration artifacts so archives do not become a catch-all warehouse of sensitive context.
- Coordinated removal across metadata stores: deletion workflows that cover content plus its associated metadata in secondary systems such as audit datasets, analytics tables, and exported administrative reports.
Integrity verification: preserve trustworthy timelines without content exposure
Incident response and audits often require proof of sequence—who accessed an asset, which systems touched it, and when key transitions occurred. Integrity support can rely on tamper-evident metadata rather than broad content access, which helps teams validate events while limiting internal exposure.
Integrity mechanisms that complement classification:- Tamper-evident event trails: append-only logging with cryptographic linkage between events so unauthorized edits to access history become detectable.
- Time discipline for metadata systems: clock synchronization and controlled timestamp sources for identity providers, mail systems, and content platforms; this reduces ambiguity in forensic timelines.
- Consistency checks on derived metadata: validation that exported or transformed assets retain the expected classification attributes (sensitivity, owner, record class) so downstream systems can trust the context even when formats change.
How to implement effective metadata classification
Effective metadata classification depends on two disciplines: consistent meaning for labels, and consistent enforcement across every place data lives and moves. When those two disciplines hold, security teams gain reliable context for controls, investigations, and compliance evidence—without constant manual interpretation.
A practical program treats metadata as both a protection asset and a privacy asset. Email headers, access logs, and cloud control-plane metadata can qualify as sensitive data even when content stays encrypted, so classification scope must cover that “metadata exhaust” from day one.
1) Establish scope that includes content and metadata exhaust
Start with a scope map that captures where security-relevant metadata originates, where it lands, and where it replicates. Content repositories matter, but so do the systems that generate high-signal metadata at scale—identity providers, mail systems, collaboration audit trails, and cloud control planes.
Scope elements that reduce blind spots:- Identity and access event streams: authentication events, group changes, entitlement grants; these records define who had access at a point in time.
- Messaging and transport metadata: email headers, routing stamps, timestamps, authentication results; this data supports phishing triage and legal review.
- Network flow metadata: source/destination, ports, timing, and volume; encryption increases the value of flow records for detection.
- Cloud instance metadata controls: enforcement state for instance metadata endpoints (for example IMDSv2 requirements) and related hardening settings; SSRF campaigns often target these surfaces for credential theft.
2) Define a classification model that maps to policy language
Build a classification model that people can understand and systems can act on. Keep label definitions short, tie each label to explicit handling rules, and define what evidence qualifies an asset for each label class.
A compact model usually includes:- Sensitivity tiers with handling rules: clear rules for access, sharing, export, and storage per tier; treat the tier as a control selector, not a descriptor.
- Regulated data categories: PII-focused definitions that align with guidance such as NIST SP 800-122, plus domain-specific categories that reflect HIPAA or financial obligations where relevant.
- Jurisdiction and retention signals: tags for residency constraints and retention schedules; GDPR enforcement trends put real scrutiny on metadata retention, not only content retention.
- Ownership intent: an accountable business owner field that routes approvals, exception review, and remediation tasks to the right group.
3) Use multiple classifiers, with confidence and conflict rules
Rely on more than one signal path. Metadata-only classification can catch exposure issues fast, while content-aware detection can separate true sensitive data from noise; the combination improves precision and reduces unnecessary restriction.
Classifier design patterns that hold up in enterprise environments:- Deterministic rules for high-certainty sources: “export from payroll system,” “customer report template,” “database dump artifact”; these rules reduce ambiguity.
- Entity and pattern detection for regulated types: models and rules that identify PII/PHI/PCI patterns, then assign classes with a confidence score.
- Context heuristics for metadata-only risk: unusual recipients, atypical routing, abnormal access times, or cross-region movement; these signals matter even when content stays unreadable.
- Conflict resolution logic: when classifiers disagree, define which signal wins, which triggers review, and which triggers temporary restriction until verification completes.
4) Tie classification to enforcement, response, and AI controls
Classification should change what systems allow. Connect labels to the same enforcement layers that already exist—identity policy engines, DLP controls, encryption policy, audit policy, and incident workflows—so labels produce concrete outcomes without extra manual steps.
Control bindings that reduce exposure windows:- Access decisions that reference labels: conditional access policies that tighten requirements as sensitivity rises (device posture, authentication strength, network location).
- Automated containment for high-risk movement: restriction or quarantine when a protected class appears in an unapproved channel or region.
- Query-time authorization for AI tools: retrieval must respect native app permissions and label-based rules at request time; this prevents answer construction from unauthorized sources.
- Response artifacts for governance: store the minimal evidence required to audit AI outputs—source references, retrieval context, and policy checks—without broad content retention.
5) Run quality loops that measure security impact, not label volume
A label program can look “complete” while it still misses the assets that matter. Measure accuracy and control outcomes: detection lift, investigation speed, and reduction in overshare events for sensitive classes.
Quality mechanisms that stay useful over time:- Precision/recall tests on curated datasets: quarterly evaluation sets per domain (HR, Finance, Support) to prevent silent decay in classifier accuracy.
- Exception aging and root-cause review: track why exceptions exist (business need, tool gap, label ambiguity) and remove systemic causes.
- Exposure-window measurement: time between risky event and containment for each sensitive class; this metric ties directly to real risk reduction.
- Drift detection on high-signal fields: monitor owner changes, repository migrations, and entitlement changes that often invalidate older labels.
6) Create shared ownership across security, IT, compliance, and business teams
Classification fails when it becomes “a security project” with no business accountability. Set decision rights for label definitions, approve exceptions through a clear workflow, and keep change control tight so label meaning stays stable across audits and tool changes.
Operating model components that prevent churn:- A label governance owner with change authority: one group owns definitions, deprecations, and mapping changes across systems.
- Domain stewards with escalation paths: HR and Finance stewards resolve edge cases fast and reduce backlog for security teams.
- Incident playbooks that reference labels: response steps vary by class—notification paths, legal review, and containment actions should follow the classification model.
- Documentation that matches day-to-day work: short handling rules embedded in the tools people use, plus a single reference guide for audits and policy review.
Metadata classification is not a one-time project — it is an ongoing discipline that matures alongside the data environment it protects. The organizations that treat metadata as a first-class security asset, rather than an afterthought, build the foundation for faster detection, stronger compliance posture, and trustworthy AI experiences. Request a demo to explore how we can help you put that foundation to work across your enterprise.